Threat Newsletter March 23, 2026

This week’s threat landscape highlights a sharp mix of ransomware and extortion pressure, credential-driven breaches, and active exploitation of high-impact enterprise and management-plane vulnerabilities. Healthcare and service providers remain prime targets, while phishing and social engineering continue to enable account takeovers and sensitive data exposure. At the same time, defenders should plan for growing fraud and intrusion capacity as deepfake-enabled social engineering and AI-assisted offensive workflows accelerate.
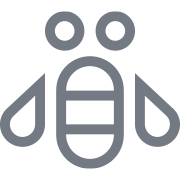
Payload Ransomware Targets Healthcare: Royal Bahrain Hospital Hit
Payload Ransomware claims it breached Royal Bahrain Hospital and stole about 110 GB of data.
Key Takeaways
New Ransomware Group: Payload Ransomware says it posted proof on its Tor leak site regarding breaching Royal Bahrain Hospital and is threatening to publish the data if a ransom is not paid by March 23.
Why it matters: Healthcare breaches can quickly become patient data exposure + operational disruption risks, and “proof posted” often signals high likelihood of follow through if not mitigated.
Hackers Breach Loblaw Network Segment, Access Basic Customer Records
Loblaw disclosed an ongoing investigation into a breach where threat actors accessed a contained, non-critical segment of its IT network that stored customer records. The company says basic contact information was exfiltrated, while passwords, payment card data, and health or pharmacy data were not impacted.
Key takeaways
What was exposed: Customer names, email addresses, and phone numbers.
What was not exposed (per Loblaw): Passwords, credit card/payment data, and health/pharmacy information.
Why it matters: Stolen contact info often fuels phishing and smishing campaigns.
User action: Be cautious of messages claiming to be from Loblaw, and avoid clicking links or sharing login details.

Telus Digital Investigates Breach Amid 1 Petabyte Data-Theft Claim
Telus Digital confirmed it is investigating a security incident after ShinyHunters claimed a multi-month breach and theft of nearly 1 petabyte of data. The alleged dataset includes a wide mix of information tied to Telus Digital’s BPO operations and, reportedly, some Telus telecom-related call records. Telus says it has engaged forensics support, is working with law enforcement, and is notifying impacted customers as its investigation continues.
Key takeaways
Who: ShinyHunters claims responsibility; Telus Digital confirmed an incident.
Scale (unconfirmed): Threat actor claims ~1 PB stolen. The total size has not been independently verified.
Why it matters: BPO providers can be high-impact targets because they may store or access data for many customer organizations.
Initial access claim: ShinyHunters alleges it used Google Cloud credentials found in data from the Salesloft/Drift breach, then searched data for more secrets to pivot further.
Extortion: ShinyHunters reportedly demanded $65M; a source indicated Telus was not engaging.
Defender note: Expect potential downstream impacts to customer environments and increased risk of credential exposure, targeted phishing, and fraud tied to support/call-center datasets.

Attempted Breach at Poland Nuclear Research Institute Blocked by Security Controls
Poland’s National Center for Nuclear Research (NCBJ) reported an attempted cyberattack targeting its IT infrastructure. The institute says security systems and internal procedures detected and blocked the activity before systems were compromised, and operations of the MARIA research reactor were not impacted.
Key takeaways
Outcome: Attempted attack was thwarted, with no confirmed system integrity compromise reported.
Operational impact: NCBJ says the MARIA reactor continued operating safely.
Attribution: No official attribution. Reporting cited possible Iran-linked indicators, but investigators cautioned they could be false flags.
Response actions: Authorities notified, investigation opened, and internal teams placed on high alert.
Why it matters: Even unsuccessful activity against nuclear/critical research organizations is high-signal and may indicate follow-on attempts against related government or energy-sector targets.
Starbucks Reports Employee Data Breach After Partner Central Phishing Attack
Starbucks disclosed a breach affecting employee (“partner”) accounts in its Partner Central portal after attackers used a phishing campaign with fake lookalike sites to steal credentials. Starbucks says its corporate network was not directly compromised, but the unauthorized access may have exposed employee personal data, and impacted employees are being offered identity protection services.
Key takeaways
How it happened: Phishing + credential theft led to unauthorized access to Partner Central accounts.
Who was impacted: Nearly 900 employees (per a filing with the Maine AG).
What data may be exposed: Name, Social Security number, date of birth, and bank account/routing details (per employee notifications).
Timeline: Unauthorized access occurred between Jan 19 and Feb 11, and Starbucks detected the issue on Feb 6.
Why it matters: This is a high-risk identity-theft dataset. Expect W-2/payroll scams, account takeover attempts, and targeted phishing.
Defender note: Reinforce anti-phishing controls, enforce MFA on employee portals, and monitor for credential reuse across SSO and payroll/benefits tooling.
The New Wave of Deepfake Fraud: Voice Clones, Fake Videos, Real Losses
Deepfake-enabled fraud is accelerating as attackers use AI to convincingly impersonate people through voice, video, images, and text. IBM highlights how businesses are seeing growing losses from deepfake calls to bypass voice authentication, social engineering of help desks and finance teams, and AI-altered documents used to defeat KYC/AML controls.
Key takeaways
Where it’s hitting: Call centers and internal help desks are prime targets for voice-clone social engineering.
Common uses: Impersonating executives, bypassing bio-metrics, generating convincing phishing text at scale, and submitting AI-altered documents for account opening and fraud.
Why it’s growing: Deepfake tools are cheaper and easier to use, lowering the barrier for attackers.
Business impact: Financial theft, account takeovers, identity fraud, and reputational damage.
Defender note: Treat voice as a weak factor. Add out-of-band verification, strengthen help desk identity proofing, harden KYC/AML workflows, and adopt multi-modal deepfake detection (audio/video/image/text) where it supports business processes.

EU Sanctions iSoon and Other Firms for Supporting Cyberattacks in Europe
The European Council imposed sanctions on three companies (two in China, one in Iran) for allegedly supporting or carrying out cyberattacks affecting European countries. The sanctioned entities include Integrity Technology Group and Anxun Information Technology (iSoon), plus the Iranian firm Emennet Pasargad. The measures restrict doing business in the EU, freeze EU-based assets, and include travel bans for iSoon’s founders.
Key takeaways
Who was sanctioned: Two China-based firms (Integrity Technology Group, iSoon) and one Iran-based firm (Emennet Pasargad), plus two iSoon founders.
Why: Alleged support for, or execution of, cyberattacks impacting European targets.
What sanctions do: Ban EU business, freeze EU assets, and impose travel restrictions on named individuals.
Why it matters: Highlights the use of “private” companies as state-linked cyber capability providers and signals increased regulatory risk for vendors tied to offensive cyber operations.
Defender note: Sanctions rarely stop operations outright, but they can constrain funding, infrastructure, and partnerships. Track associated infrastructure and TTPs for potential follow-on activity and targeting.

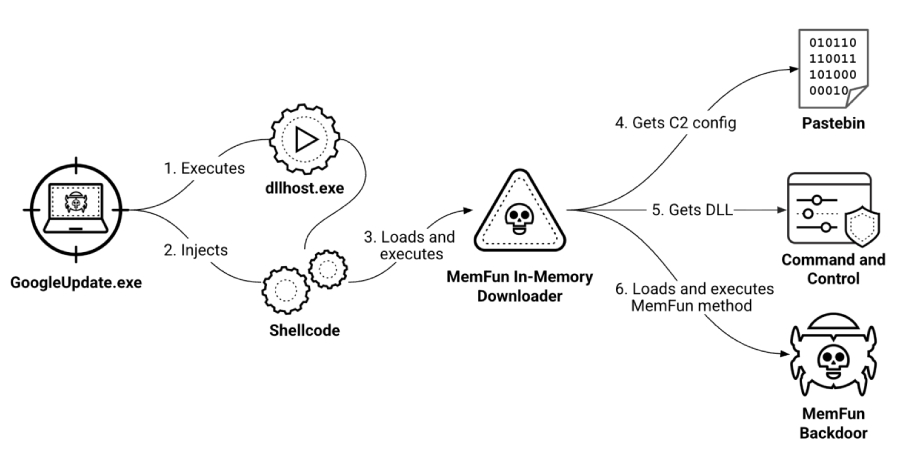
China-Linked Threat Actors Used Novel Backdoors to Persist in Southeast Asia Military Targets
Palo Alto Networks Unit 42 reported a long-running cyber espionage campaign targeting Southeast Asian military organizations, attributed with moderate confidence to China-nexus actors (tracked as CL-STA-1087). The activity dates back to at least 2020 and used novel backdoors and stealth techniques, including abuse of legitimate cloud/content services for command-and-control.
Key takeaways
Who/track: Unit 42 attributes the cluster to China-nexus actors with moderate confidence; tracked as CL-STA-1087.
Targets: Southeast Asian military organizations, focused on intelligence collection (not smash-and-grab theft).
Tools: New backdoors AppleChris and MemFun, plus a customized Getpass credential stealer.
Stealth & C2: Used dead-drop resolvers and legitimate services like Pastebin and Dropbox to hide C2, plus evasion like delayed execution and timestomping.
Why it matters: Long-dwell, high-discipline access suggests ongoing collection and potential follow-on operations against partner networks.
Defender note: Tighten controls/monitoring for “legit” services (Pastebin/Dropbox) if not business-required, and hunt for suspicious PowerShell, timestomping, and published IOCs.
New DarkSword iOS Exploit Kit Enables Full Device Takeover via Zero-Day Chain
Researchers reported a full-chain iOS exploit kit dubbed DarkSword that has been used since at least Nov 2025 by multiple actors, including commercial surveillance vendors and suspected state-linked operators. The kit chains six vulnerabilities (including three zero-days at the time) to gain privileged access on iPhones and rapidly steal a broad set of sensitive data, often via watering-hole style delivery through compromised websites.
Key takeaways
What it is: A full iOS exploit chain + infostealer (JavaScript-based) capable of full device takeover and fast data theft.
Who’s using it: Multiple clusters tied to espionage and commercial surveillance (e.g., UNC6353, UNC6748, and activity linked to PARS Defense).
Targets observed: Campaigns targeting users in Saudi Arabia, Turkey, Malaysia, and Ukraine.
How it works (high level): Web delivery via Safari → sandbox escapes → privilege escalation → data harvesting modules → exfiltration.
Vulns/patching: Chains 6 CVEs; 3 were zero-days before Apple patches (notably CVE-2026-20700, CVE-2025-43529, CVE-2025-14174). Ensure iOS devices are fully updated.
Why it matters: Demonstrates rapid exploit proliferation across actors and high risk to executives, journalists, dissidents, and high-value mobile users.
Defender note: Prioritize iOS patch compliance, monitor for watering-hole exposure, and consider mobile threat defense for high-risk users.

Okta Helps Takedown ShieldGuard Infrastructure Used for Crypto Wallet Theft
Okta Threat Intelligence reported disrupting “ShieldGuard,” a crypto scam that promoted a browser extension marketed as wallet protection. Analysis showed the extension was designed to harvest wallet addresses and exfiltrate sensitive page content from major crypto platforms (and some Google services), enabling theft and fraud. Okta and partners worked to remove the extension and disrupt its command-and-control infrastructure.
Key takeaways
What it was: A malicious Chrome extension posing as a crypto wallet security tool.
Lure: Multi-level marketing + airdrop incentives to drive installs.
Data theft behavior:
- Harvested wallet addresses via EIP-6963 wallet discovery.
- Exfiltrated full page HTML (potentially balances and transaction history) from sites like Binance, Coinbase, OpenSea, Uniswap.
Control & evasion: Contacted a C2 at shieldguards[.]net to fetch scripts and run arbitrary code, while tracking users with persistent UUIDs.
Disruption actions: Extension removed from Chrome Web Store, domain/hosting/registrar actions taken to cut off C2, and sign-in functionality disabled.
Defender note: Enforce extension allowlisting on managed browsers, minimize plugins on high-risk workflows (finance/crypto), and monitor for suspicious traffic to content hosting/C2 infrastructure.
North Korea’s Fake IT Worker Network Funnels $500M a Year and Infiltrates Western Firms
Researchers (IBM X-Force and Flare) detailed how North Korea-backed “fake IT worker” schemes place remote workers into Western companies using false or borrowed identities. Beyond generating revenue for the regime, these placements can also enable access to sensitive systems and data.
Key takeaways
Scale & funding: US government estimates suggest up to ~100,000 workers across many countries, generating ~$500M/year.
How the scheme works: An ecosystem of recruiters, facilitators, workers, and Western collaborators/brokers helps candidates obtain jobs and maintain access.
Tradecraft indicators: Use of stolen/synthetic identities, heavy reliance on translation tools, and coordination tooling (reported examples include North Korea-linked VPN tooling and lightweight messaging).
Why it matters: This is an insider access problem. Once hired, workers can gain privileged access and potentially support data theft or follow-on compromise.
Simple defensive steps: Strengthen remote hiring verification (identity and location checks), watch for interview anomalies (face/voice manipulation), validate resume claims, and require managed devices and least privilege for new hires.

AI Outscores 99% of Humans in Elite Hacking Competitions
A report claims a startup’s AI system outperformed more than 99% of approximately 125,000 human competitors across six elite capture-the-flag (CTF) hacking competitions. The result suggests AI is increasingly capable at solving vulnerability-style challenges that resemble real-world attacker workflows.
Key takeaways
What happened: AI reportedly placed in the top 1% across six CTF events.
Why it matters: Strong CTF performance can translate into faster bug finding, exploit-chaining, and automation of repetitive attacker steps.
Defender impact: Expect shorter “time-to-exploit,” with more opportunistic scanning and faster weaponization once bugs are known.
Simple actions: Tighten patch SLAs for internet-exposed services, reduce exposed attack surface, and ensure detections cover exploit chains (web → privilege escalation → credential/data access).

FBI/CISA Alert: Signal Account Takeovers Using Fake “Security Support” Messages
FBI and CISA warned of a phishing campaign attributed to Russian intelligence services that targets Signal users by stealing authentication codes or getting victims to scan malicious QR codes. Rather than breaking encryption, the actors aim to take over accounts by abusing Signal’s linked devices feature, giving them access to messages, groups, and contacts.
Key takeaways
The weakness isn’t encryption: The campaign focuses on social engineering and account takeover, not cryptographic compromise.
How it works: Fake “Signal Security/Support” messages create urgency and request an SMS code or QR scan to “verify” the account.
What attackers gain: Access to conversations and groups, plus the ability to impersonate the victim and phish trusted contacts.
Who is targeted: High-value individuals (government, military, political figures, journalists), but tactics can spread broadly.
Simple defenses: Never share verification codes, never scan unsolicited QR codes, and routinely check Signal’s linked devices list and remove anything unknown.

Oracle Releases Emergency Patch for Critical Oracle Identity Manager RCE (CVE-2026-21992)
Oracle released an out-of-band security update for CVE-2026-21992, a critical, unauthenticated remote code execution (RCE) vulnerability affecting Oracle Identity Manager and Oracle Web Services Manager. With a CVSS 9.8 rating and no required authentication, exposed systems could be fully compromised if not patched quickly.
Key takeaways
Severity: Critical (CVSS 9.8) and remotely exploitable with no auth and no user interaction.
Affected products: Oracle Identity Manager (REST Web Services) and Web Services Manager (Web Services Security), including versions 12.2.1.4.0 and 14.1.2.1.0.
Impact: Successful exploitation could enable full system takeover, credential theft, and lateral movement.
What to do now: Apply Oracle’s patches immediately and prioritize any internet-facing middleware endpoints.
Mitigation while patching: Review and restrict HTTP/HTTPS exposure to the affected services, and monitor for suspicious requests to the relevant web service endpoints.

CISA Warns Cisco Firewall Management 0-Day Is Being Exploited in Ransomware Attacks (CVE-2026-20131)
CISA warned that CVE-2026-20131 is being actively exploited in ransomware campaigns targeting Cisco firewall management products. The flaw is an unauthenticated deserialization issue in the web management interface that can allow remote code execution as root, making it a high-risk path to rapid network compromise.
Key takeaways
What’s vulnerable: Cisco Secure Firewall Management Center (FMC) and Security Cloud Control (SCC) Firewall Management.
Exploit impact: Unauthenticated remote root RCE via deserialization of untrusted data (CWE-502).
Why it matters: Management consoles provide centralized control. Compromise can enable policy tampering, lateral movement, and fast ransomware deployment.
Status: Added to CISA’s Known Exploited Vulnerabilities (KEV) catalog due to active exploitation.
What to do now: Apply Cisco’s fixes/mitigations immediately. If patching is delayed, restrict access to the management interface (IP allowlists/VPN/admin network only) or take it offline until secured.

Active Exploitation: Microsoft SharePoint RCE Vulnerability CVE-2026-20963
CISA warned that CVE-2026-20963, a critical SharePoint Server vulnerability patched in January 2026, is now being exploited in the wild. The flaw is an unauthenticated deserialization issue that can allow attackers to achieve remote code execution (RCE) on unpatched on-prem SharePoint servers.
Key takeaways
What’s vulnerable: SharePoint Enterprise Server 2016, SharePoint Server 2019, and SharePoint Server Subscription Edition.
Exploit impact: Unauthenticated RCE in low-complexity, network-based attacks (deserialization of untrusted data).
Also at risk: SharePoint 2007/2010/2013 are vulnerable but end-of-support. Upgrade is required (no patches).
Status: Added to CISA’s Known Exploited Vulnerabilities (KEV) catalog, with an urgent patch deadline for US federal agencies.
What to do now: Patch immediately, audit for any exposed SharePoint servers, and reduce external exposure where possible.

Patch Now: ScreenConnect Vulnerability Exposes Machine Keys, Enables Auth Bypass
ConnectWise warned of a critical ScreenConnect vulnerability (CVE-2026-3564) that could allow attackers to extract server-level machine keys and then forge or manipulate session authentication, enabling session hijacking and access bypass. The issue affects on-prem ScreenConnect deployments prior to 26.1; cloud-hosted instances have already been mitigated by ConnectWise.
Key takeaways
Severity: CVSS 9.0 (critical-to-important range), priority 1 advisory.
What’s vulnerable: ScreenConnect versions prior to 26.1 (on-prem).
What can happen: Attackers can extract machine keys and impersonate/hijack sessions by forging auth tokens.
Why it matters: Remote access tooling is high-value. Compromise can lead to rapid lateral movement and follow-on ransomware/credential theft.
What to do now: Upgrade to ScreenConnect 26.1 immediately, and audit for anomalous authentication/session activity.

LeakNet Ransomware Abuses ClickFix Lures to Deliver In-Memory Payloads
LeakNet ransomware operators are using the ClickFix social engineering technique via compromised websites to trick users into manually running malicious commands (often framed as fixing a fake error). Once executed, the intrusion chain can deploy a Deno-based in-memory loader that stages additional payloads with limited on-disk artifacts, leading into a repeatable post-exploitation sequence that can culminate in ransomware.
Key takeaways
Initial access: Compromised sites show fake CAPTCHA/verification prompts that instruct users to run a malicious msiexec command.
Execution technique: Uses a Deno (JavaScript runtime) loader to run Base64-encoded JavaScript in memory, reducing disk evidence.
Why it matters: This “wide net” technique reduces reliance on initial access brokers and can scale quickly.
Post-compromise pattern: Observed sequences include DLL side-loading, lateral movement via PsExec, data exfiltration, then encryption.
Defender note: Alert on unusual msiexec from Run dialogs, hunt for Deno/BYOR runtime usage, and watch for PsExec + klist activity and suspicious outbound traffic to cloud storage (e.g., S3).

New SILENTCONNECT Loader Deploys ScreenConnect Using PEB Masquerading and UAC Bypass
SILENTCONNECT is a multi-stage malware loader observed since at least March 2025 that uses phishing and living-off-the-land techniques to install ConnectWise ScreenConnect for hands-on remote access. It relies on VBScript and in-memory PowerShell execution, then uses PEB masquerading and a UAC bypass to evade defenses and establish persistent control.
Key takeaways
Initial access: Phishing link → fake Cloudflare Turnstile CAPTCHA → downloads a VBScript lure (e.g., “E-INVITE.vbs”).
Execution chain: VBScript triggers in-memory PowerShell that downloads/compiles a C# loader at runtime (minimal on-disk artifacts).
Defense evasion: Uses PEB masquerading (spoofs process/module names like winhlp32.exe) to hide from EDR that relies on PEB metadata.
Privilege & persistence: Performs a UAC bypass and adds Microsoft Defender exclusions before installing ScreenConnect.
Impact: ScreenConnect gives attackers full interactive control, enabling credential theft, lateral movement, and follow-on ransomware.
Defender note: Alert on VBScript-from-internet + PowerShell Add-Type, unexpected Defender exclusion changes, msiexec installing ScreenConnect, and outbound connections to unknown ScreenConnect servers (notably TCP/8041).