Threat Newsletter April 6, 2026

This week’s newsletter centers on how attackers (and platforms) are increasingly using “quiet” collection and trust abuse to gain leverage—ranging from subtle tracking and data leakage (like extension fingerprinting and exposed API keys), to high-impact compromises and extortion, to social-engineering and supply-chain tactics that turn everyday tools and user actions into the entry point—reinforcing the need for tight hygiene (secrets/patching) and guardrails against user-execution scams.
LinkedIn Under Fire Over Covert Extension-Detection Tracking on Chromium Browsers
The article reports findings from a “BrowserGate” investigation claiming LinkedIn includes hidden JavaScript that detects which browser extensions a person has installed (on Chromium-based browsers) and sends that data back to LinkedIn (and, per the report, to third parties).
Key Takeaways
Hidden tracking claim: LinkedIn allegedly checks your browser for installed extensions without clearly telling you.
Who it affects: Reportedly targets Chromium browsers (Chrome, Edge, Brave, Opera, Arc), not Firefox/Safari.
Why it matters: Your extensions can reveal sensitive info (job searching, political/news tools, religion, disability aids, etc.).
Org risk: If tied to real identities + employers, extension scans could map what tools entire companies use (competitive intel).
Quick mitigations suggested: Use Firefox/Safari for LinkedIn, or a separate “LinkedIn-only” browser profile with no extensions installed.

FBI Director’s Personal Inbox Hacked as Handala Publishes Emails, Photo
Iran-linked hackers known as the “Handala Hack Team” allegedly gained access to FBI Director Kash Patel’s personal email account and then published material online, including emails and personal documents/photos.
Key Takeaways
Executive “personal” compromise still matters: Even if government systems weren’t breached, personal email can reveal contacts, travel, habits, and communications that enable follow-on targeting.
Likely information-ops / embarrassment angle: Publishing content publicly suggests the goal is reputational damage and influence, not quiet espionage.
“Historical” data can fuel current attacks: Older emails/docs can still support phishing pretexts, credential reset attempts, and social engineering against colleagues and partners.
Highlights leadership OPSEC gaps: Senior leaders are high-value targets; strong MFA, account hygiene, and separation of personal vs. work communications are critical to reduce blast radius.
Iran-linked threat activity context: Reporting connects Handala to Iran-linked activity amid heightened geopolitical tensions, underscoring the increased likelihood of public-facing leaks and retaliatory cyber activity.

API Keys Left in the Open: Mass Web Scan Finds Widespread Secret Leakage
Researchers analyzed a large sample of the public web (reported as 10 million webpages) and found that API credentials are frequently exposed in publicly accessible website content—often in client-side resources like JavaScript—creating a “quiet” but high-impact path to compromise because the leaked keys can grant programmatic access to cloud services and other critical systems.
Key Takeaways
Public web pages still leak secrets at scale: Even basic web content can contain live API keys/tokens, not just GitHub repos or paste sites.
JavaScript is a major leakage point: Client-side JS resources are repeatedly called out as a common place where credentials end up exposed.
API keys are “high leverage” credentials: Unlike a single-user password, API keys often enable automated access to data, cloud infrastructure, payment/DevOps platforms, and can lead to broad impact (data access, abuse of services, supply-chain risk).
The risk can persist for a long time: Keys may not expire automatically, so exposures can remain usable until detected and rotated/revoked.
Practical defensive focus: Treat secret scanning and key rotation as continuous hygiene—scan web assets/build outputs, avoid shipping secrets to the browser, and rotate/revoke exposed keys quickly
API Keys Left in the Open: Mass Web Scan Finds Widespread Secret Leakage
Researchers analyzed a large sample of the public web (reported as 10 million webpages) and found that API credentials are frequently exposed in publicly accessible website content—often in client-side resources like JavaScript—creating a “quiet” but high-impact path to compromise because the leaked keys can grant programmatic access to cloud services and other critical systems.
Key Takeaways
Public web pages still leak secrets at scale: Even basic web content can contain live API keys/tokens, not just GitHub repos or paste sites.
JavaScript is a major leakage point: Client-side JS resources are repeatedly called out as a common place where credentials end up exposed.
API keys are “high leverage” credentials: Unlike a single-user password, API keys often enable automated access to data, cloud infrastructure, payment/DevOps platforms, and can lead to broad impact (data access, abuse of services, supply-chain risk).
The risk can persist for a long time: Keys may not expire automatically, so exposures can remain usable until detected and rotated/revoked.
Practical defensive focus: Treat secret scanning and key rotation as continuous hygiene—scan web assets/build outputs, avoid shipping secrets to the browser, and rotate/revoke exposed keys quickly.
Fake Cloudflare Verification Page Used to Deploy Python-Based Infiniti Stealer on Macs
A macOS-focused ClickFix campaign is using a fake Cloudflare-style “human verification”/CAPTCHA page to social-engineer victims into pasting and running a “verification” command in Terminal.
Key Takeaways
ClickFix is a user-execution technique: No exploit needed—success depends on convincing the user to run a command in Terminal.
Cloudflare branding increases trust: The fake “verification” page imitates a legitimate Cloudflare check to lower suspicion.
Multi-stage chain with defense evasion: Bash stager → loader → final stealer; removes quarantine flag and uses randomized delays / analysis-environment checks.
Data theft scope is broad: Browsers + Keychain + crypto wallets + developer secrets + screenshots high risk for both individuals and orgs.
Trend signal: Windows-proven social engineering tradecraft is being adapted effectively to macOS, so Mac fleets need the same “assume-user-will-be-tricked” posture (controls + training).
Low-Privilege WordPress Users Can Read Sensitive Files via Smart Slider 3 Export Bug
A vulnerability in the Smart Slider 3 WordPress plugin (CVE-2026-3098) allows any authenticated user even a low-privilege “subscriber” to read arbitrary files on the server by abusing the plugin’s AJAX export functionality.
Key Takeaways
Low-privilege user → high impact: Only authentication is required; subscriber-level access can be enough to read sensitive server files.
Credential exposure is the real danger: Reading wp-config.php can hand over database credentials plus WordPress secret keys/salts—often a stepping stone to broader compromise.
Root cause: missing authorization checks: The export action lacked proper capability checks and file validation, so authenticated users could abuse it.
Update now: Fixed in 3.5.1.34; risk persists mainly because of lagging plugin updates across large install bases.
Exposure is higher on “membership” sites: Any WordPress site that allows user registration/subscriptions is more directly exposed to this auth-required bug.

Axios npm Backdoor Attributed to North Korea-Linked UNC1069, Google Says
Google/GTIG attributed the Axios npm supply-chain compromise to a North Korea–linked cluster tracked as UNC1069.
Key Takeaways
This is a “trust chain” attack, not an Axios code bug: The distribution channel/maintainer publishing path was abused.
Massive downstream blast radius: Axios is extremely widely used, so a short compromise window can still impact huge numbers of installs across CI/CD and developer endpoints.
Developer + CI systems are the real targets: Once a build environment is hit, attackers can steal credentials (cloud keys, tokens) and pivot into production/SaaS environments.
Credential theft enables follow-on supply-chain attacks: Stolen secrets from one event can be recycled to compromise more packages and organizations (cascading effect).
Practical response: Identify whether the malicious versions were installed, rotate any exposed secrets, and use published IoCs/hunting rules to check endpoints and build runners for RAT activity.
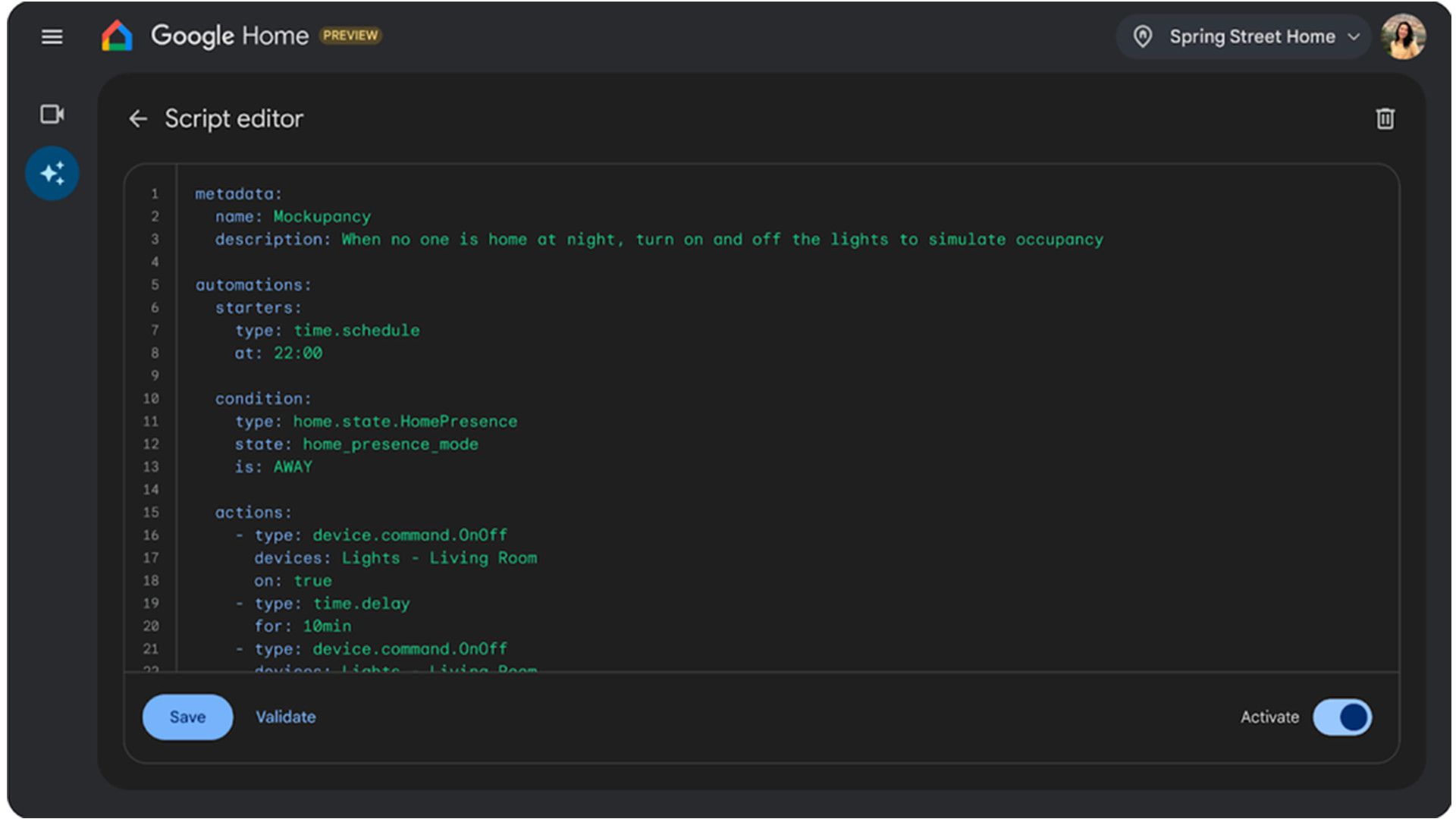
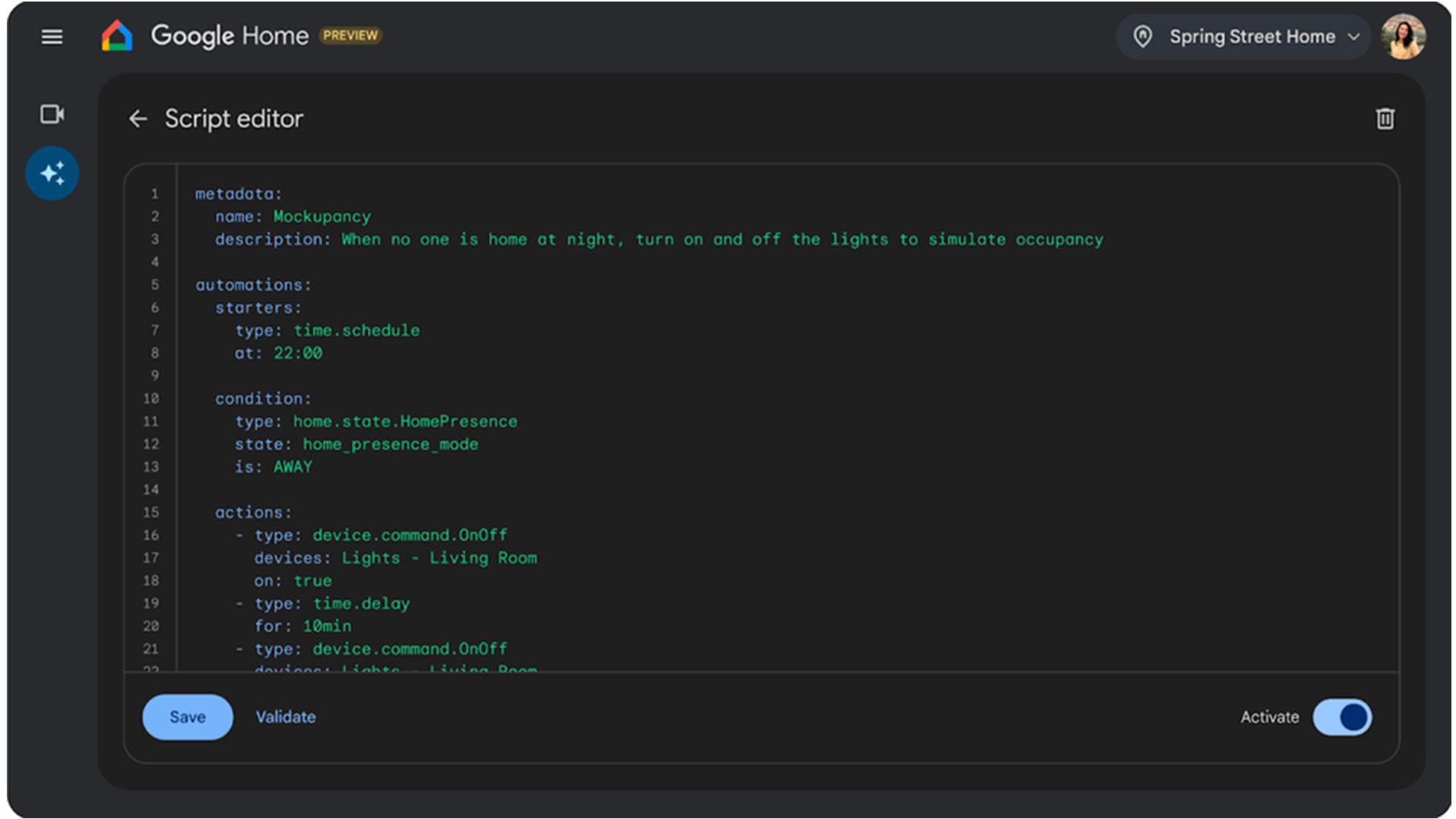
New macOS Feature Flags Suspicious Terminal Paste Commands Used in ClickFix Attacks
Apple is adding a macOS security feature in macOS Tahoe 26.4 that warns users when they paste certain potentially harmful commands into Terminal to blunt “ClickFix” style social engineering where attackers trick people into running copy/pasted commands that download infostealers.
Key Takeaways
ClickFix is social engineering, not an exploit: The attacker’s “payload” is getting the user to run a command in Terminal.
New macOS guardrail targets the exact behavior: It intervenes at the moment of copy/paste into Terminal, where these scams commonly succeed.
Still user-decision dependent: The feature helps only if users stop and don’t click through (e.g., “Paste Anyway”) out of habit/urgency.
Attackers will likely adapt: ClickFix campaigns continuously change lures and commands to evade defenses, so organizations should treat this as one layer, not a complete solution.
Best practice stays the same: Don’t run pasted commands from untrusted sources; verify instructions independently; maintain endpoint/web protections and user awareness training.

CVE-2026-3055: Active Exploitation Targets Citrix NetScaler ADC/Gateway
CVE-2026-3055 is a high-severity vulnerability affecting Citrix NetScaler ADC and Gateway that has been actively exploited since March 27, 2026
Key Take Takeaways:
High impact data exposure: A memory over-read can leak sensitive information from affected systems, which can become a pivot point for broader compromise.
Patch management is the main control: The practical “fix” is immediate patching/updates from Citrix plus tight vulnerability management process.
Use layered detection while patching: Monitor for anomalous access patterns and suspicious activity around NetScaler, because exploitation may already be underway.
Password Problems in Manufacturing and Healthcare Keep Fueling Ransomware
Manufacturing and healthcare have a similar security problem: weak password habits. People often reuse passwords, keep them too simple, or even share logins because speed and uptime matter more day-to-day than security.
Key Takeaways
High ransomware pressure: Manufacturing and hospitals can’t afford downtime, so they’re prime targets.
Weak password habits: Shared logins + reused/simple passwords are common for speed.
Legacy tech drag: Older systems make modern login controls harder to implement quickly.
Culture gap: Security feels like it slows work down (“you’re slowing me down”).
Quick wins: watch for suspicious logins and enforce basics (no sharing, no reuse).
Silver Fox Threat Group Expands Regional Campaign With AtlasCross RAT
Silver Fox (a China-based threat actor) is expanding cyber activity across Asia by using fake lookalike domains (typosquatting) that impersonate popular tools via Zoom, Signal, and Teams.
Key Takeaways
Delivery = fake “brand” sites: The campaign leans on typo/lookalike domains to get users to download malware while thinking it’s a real app or update.
Payload = remote access: AtlasCross RAT gives attackers hands-on access (remote control + data theft), which can become a stepping stone to deeper compromise.
“Looks legit” is part of the strategy: Reporting notes signed installers and other trust signals used to reduce suspicion and increase install success.
Blended ops model: Silver Fox runs both broad, opportunistic campaigns and more advanced operations, and keeps evolving tooling over time.
Defensive focus: treat new/unknown download domains as hostile, verify software sources, and hunt for unusual remote-access behaviors (especially in-memory execution and security-tool tampering) tied to “installer” activity.

Up to 270M iPhones at Risk: Apple Issues iOS 18 Security Patch for DarkSword
Apple issued an unusual “backported” security update for iOS 18 to protect users from the DarkSword exploit chain, instead of forcing everyone onto the newest iOS version.
Key Takeaways
Big iPhone exploit is spreading: DarkSword can silently compromise iPhones on iOS 18 (e.g., via malicious websites).
Apple made a rare move: Apple is shipping an iOS 18 security patch (backport) even for devices that could upgrade to iOS 26.
Huge potential exposure: the article cites estimates of roughly 221M–270M devices potentially vulnerable.
Why it matters: exploit code reportedly circulated more widely, making it easier for more threat actors to reuse.
Action: install the iOS 18 security update ASAP (or upgrade to the latest iOS for broader protections).

Hackers Claim 3M Cisco Salesforce Records, GitHub Repos, and AWS Data in Extortion Push
ShinyHunters is pressuring Cisco with threats after claiming they stole a large cache of Cisco-related data, including over 3 million records from Cisco’s Salesforce environment (PII), plus other internal assets like GitHub repositories and AWS data.
Key Takeaways
Extortion pressure: ShinyHunters is trying to force payment by threatening “annoying” consequences / release of data.
Alleged data scope is broad: ~3M Salesforce records with personal data, plus GitHub repos and AWS-related data (per the actor’s claim).
Multiple intrusion paths claimed: The actor suggests the data came from more than one breach vector (vishing/social engineering, a Salesforce Aura-related issue, and AWS compromise).
Customer risk = follow-on attacks: If customer PII and internal details are real, it can enable targeted phishing, fraud, and impersonation against Cisco customers and partners.
Key defender lesson: SaaS/CRM data is a prime target—protect it like production (strong identity controls, anti-vishing training, tight access, and monitoring for unusual exports/downloads).

AI Startup Mercor Confirms Incident Linked to LiteLLM Supply-Chain Attack
Mercor confirmed it experienced a security incident tied to a supply-chain compromise of the open-source LiteLLM project. Mercor said it was “one of thousands” potentially impacted after malicious code was found in a LiteLLM-associated package (and removed within hours), while the extortion group Lapsus$ separately claimed it targeted Mercor and posted a sample of allegedly stolen data that included references to Slack and ticketing data.
Key Takeaways
Supply-chain risk is the headline: a compromise in a widely used open-source library can hit many downstream companies fast.
Mercor confirmed impact: They say they were affected and moved quickly to contain/remediate, with an ongoing forensic investigation.
Lapsus$ is adding pressure: The group claimed a Mercor breach and posted samples; TechCrunch reviewed samples referencing internal-style data (e.g., Slack/ticketing).
Details are still unclear: It’s not confirmed how the stolen data (if authentic) was obtained or what the true scope of exposure is yet.
Defender lesson: Treat developer dependencies as production attack surface (pin/verify packages, monitor CI/CD and installs, and be ready to rotate secrets if a build environment is suspected compromised).

Hasbro Confirms Cyber Incident, Implements Workarounds to Keep Orders Moving
Hasbro disclosed it detected unauthorized access to its network around March 28, 2026 and responded by taking some systems offline while it investigates with external cybersecurity support.
Key Takeaways
Confirmed intrusion: Hasbro reported unauthorized network access and launched an incident response + investigation.
Systems taken offline: They proactively shut down some systems to contain the incident.
Business impact: Order processing and shipping can be affected; delays are possible.
Timeline: Hasbro warned interim measures and recovery may take “several weeks.”
Data impact not final yet: They’re still determining scope and reviewing potentially impacted files.

Venom Stealer Raises the Stakes: ClickFix Delivery, Continuous Data Theft
Venom Stealer is a new malware-as-a-service (MaaS) infostealer that “productizes” ClickFix social engineering (fake verification/update pages that trick users into pasting commands into Run/Terminal).
Key Takeaways
ClickFix delivery: Fake Cloudflare CAPTCHA / fake updates / fake SSL errors trick users into pasting a command into Run or Terminal.
Fast credential + wallet theft: Immediately harvests browser data and crypto wallet vaults across browser profiles.
Automated “steal → crack → drain”: Stolen wallet data is sent to cracking infrastructure and, if cracked, funds can be swept quickly (multi-chain).
Harder IR problem: It can keep running and keep stealing newly saved credentials (so rotating passwords alone may not be enough if the endpoint is still infected).
Best defenses: Stop the paste-and-run behavior (training + restrict PowerShell/Run dialog where possible) and watch/block suspicious outbound data exfiltration.

WhatsApp Social Engineering Drives Stealthy VBS-to-MSI Infection Chain on Windows
Microsoft reports a campaign (seen starting late Feb 2026) where attackers use WhatsApp messages to trick users into running malicious VBScript (VBS) files.
Key Takeaways
Initial access: WhatsApp messages deliver malicious .vbs files (social engineering, not a software exploit).
Living-off-the-land evasion: The script drops legit Windows utilities but renames them (ex: curl.exe renamed to netapi.dll, bitsadmin.exe renamed to sc.exe) to blend in.
Payloads hosted on trusted cloud: Secondary VBS stages are downloaded from AWS S3, Tencent Cloud, and Backblaze B2, making traffic look “normal.”
Privilege + persistence: It tampers with UAC/registry settings and keeps retrying elevation to gain admin-level control and survive reboots.
End goal: Install unsigned MSI “backdoor” packages (some masquerade as common tools like AnyDesk/WinRAR) to maintain remote access.

Texas Hospital Reports Network Intrusion Affecting 257,073 Individuals
Nacogdoches Memorial Hospital disclosed a network intrusion that may have exposed personal and protected health information for up to 257,073 people.
Key Takeaways
Dwell time: Attacker may have had ~2 weeks inside the network (Jan 15–Jan 31).
Data types: Names/contact info plus sensitive identifiers like SSNs, DOB, medical record/account numbers, health plan beneficiary numbers, and (for some) full-face photos.
Patient risk: Even without confirmed misuse, the exposed data mix supports identity theft + medical fraud risk (so people should consider fraud alerts/credit freezes).
Response notes: Notifications were sent, security controls/training were strengthened, and no threat group had publicly claimed the incident as of April 1; the notice also says free credit monitoring was not offered.

Citrix NetScaler Under Fire: CISA Issues Official Patch Alert for CVE-2026-3055
CISA issued an official warning urging rapid patching for a critical Citrix NetScaler vulnerability (CVE-2026-3055) after it was observed being exploited in the wild.
Key Takeaways
It’s actively exploited: Attackers are using this bug right now.
High severity: Rated critical (9.3), and can leak sensitive info from the appliance’s memory.
SAML/SSO configs are key: Risk is highest when NetScaler is set up as a SAML Identity Provider.
Patch is available: Citrix released fixed versions; unpatched systems remain exposed.
CISA warning = drop everything: When CISA adds/flags something, treat it as “patch immediately,” especially for internet-facing gateways.