Threat Newsletter April 13, 2026

Last week’s stories highlight a clear trend: attackers are succeeding by moving faster than organizations can patch and by targeting the areas that most often get overlooked—third‑party software and dependencies, exposed admin/management systems, and credentials/API keys.
We’re seeing this play out in several ways: fake “lookalike” software packages that run malicious code during installation, real-world exploitation of known vulnerabilities to gain quick access, and cloud breaches where stolen API keys enable data theft—often followed by extortion.
36 Rogue npm Packages Deliver Redis RCE Malware in Supply-Chain Attack
Cybersecurity researchers (Safedep) identified a software supply-chain campaign involving 36 malicious npm packages that pretended to be Strapi plugins.
Key Takeaways
Main risk: Installing “lookalike” npm packages can lead to instant compromise via postinstall.
- Scope: 36 rogue packages, designed to blend in with Strapi plugin naming.
- Impact: RCE + persistence + data theft (secrets like
.env, private keys, database credentials, wallet data).
Techniques observed:
- Redis command abuse to write malicious files (cron/web shell/reverse shell)
- Reverse shells (multiple methods for reliability)
- Docker/container escape attempts via overlay filesystem paths
- C2 over HTTP to exfiltrate data and receive commands
Targeting signal: Evidence suggests focus on cryptocurrency-related infrastructure.
Defender actions :
- Treat new/unfamiliar packages as untrusted; verify publisher + package history
- Audit/monitor
postinstallscripts in dependencies - Lock down Redis exposure where there is no public access, authentication, least privilege, and network controls)
- Monitor build/CI environments for unexpected outbound traffic, new cron entries, and suspicious file writes.

Fortinet Under Fire: Pre-Auth Bypass Exploited in the Wild
CISA added a critical Fortinet FortiClient Enterprise Management Server (EMS) vulnerability (CVE-2026-35616) to its Known Exploited Vulnerabilities (KEV) catalog after seeing active exploitation.
Key Takeaways
What it is: CVE-2026-35616 is a vulnerability in Fortinet FortiClient EMS (CWE-284 improper access control), CVSS 9.1.
Why it matters: It’s actively exploited in the wild and allows unauthenticated (no creds) API auth bypass, which can lead to RCE/command execution.
Who is affected: FortiClient EMS 7.4.5 and 7.4.6 (the 7.2 branch is not affected).
How it’s being seen: Exploitation attempts were observed via honeypots (watchTowr reported activity starting March 31, 2026).
Exposure risk: Internet-facing EMS (especially the telemetry endpoint that’s often exposed) increases attack surface; Shadow server reported 2,000+ publicly accessible instances.
Patch: Apply Fortinet’s hotfix immediately for 7.4.5/7.4.6 and reduce exposure of EMS to the internet wherever possible.

Credential Theft at Scale: React2Shell Exploitation Goes Automated
Hackers are exploiting React2Shell (CVE-2025-55182) in vulnerable Next.js applications to run a highly automated credential/secret theft operation.
Key Takeaways
What’s happening: Automated scanning → exploit React2Shell in Next.js → drop scripts → harvest secrets → exfiltrate to NEXUS Listener C2.
Scale: Cisco Talos observed 766 compromised hosts in 24 hours.
What gets stolen: .env secrets, API keys, DB credentials, GitHub/GitLab tokens, SSH keys, AWS/GCP/Azure credentials/metadata, Kubernetes tokens, container info, command history, and runtime/process data.
Why it matters: Stolen secrets enable cloud account takeover, database/payment-system access, possible supply-chain follow-on, and lateral movement using SSH keys.
How exfiltration works: Data is sent in chunks over HTTP (port 8080) to the attacker’s NEXUS Listener server, which provides stats/search/filtering of stolen credentials.
Patch/upgrade Next.js/affected components to remediate React2Shell.
If you suspect exposure: Rotate all credentials immediately (cloud keys/tokens, DB credentials, API keys, Git tokens) and replace reused SSH keys.
- Enforce AWS IMDSv2, implement least privilege for cloud/container roles, and add WAF/RASP plus secret scanning to reduce blast radius and detect leaks faster.

TeamPCP Tied to European Commission Cloud Breach via Stolen AWS API Key
CERT-EU attributed a major European Commission breach to the hacking group TeamPCP, saying the attackers misused a secret AWS API key to access the Commission’s Europa.eu AWS environment
Key Takeaways
What happened: Attackers compromised an AWS account by misusing a secret Amazon API key, enabling unauthorized access to cloud resources and data theft.
Likely initial access path: CERT-EU assessed the intrusion originated from a supply-chain compromise of Trivy, which led to the AWS secret being exposed/obtained.
Impact / data stolen: Roughly 92GB of compressed data was exfiltrated, including names, email addresses, and some email content (notably outbound-email related files).
Scope: Potential data exposure impacted dozens of clients/entities using the affected AWS-hosted platform (reported as 42 internal clients + at least 29 EU entities).
Detection signal: The compromise was detected after alerts for abnormal Amazon API usage / potential account compromise / unusual network traffic.
Threat actor / ecosystem: CERT-EU attributed the breach to TeamPCP; stolen data later appeared on ShinyHunters’ leak site, suggesting a criminal “handoff/monetization” pipeline.
Why it matters: One leaked cloud API key can lead to major blast radius (data exfiltration + potential lateral movement across cloud accounts if permissions allow).

UNC6783 Targets BPOs to Access Zendesk Support Data for Extortion
UNC6783 is a threat actor Google tracks as targeting business process outsourcing (BPO) providers to gain downstream access to high-value companies’ support environments, especially Zendesk.
Key Takeaways
Primary target: BPOs/helpdesks as an entry point to larger enterprises.
What they steal: Zendesk support tickets / sensitive support data used for leverage in extortion.
How they get in: Live-chat social engineering + phishing, pushing staff to spoofed Okta pages on lookalike domains.
MFA bypass angle: The phishing kit can steal clipboard contents (to help defeat MFA) and enable attacker device registration.
Post-compromise: Data theft followed by extortion demands (reported via ProtonMail accounts).
Defender focus areas: Use FIDO2 security keys, monitor/support-live-chat for abuse, block Zendesk-lookalike domains, and audit MFA device enrollments regularly.

Ex-Engineer Pleads Guilty After Locking Admins Out of Hundreds of Servers in Ransom Scheme
A former core infrastructure engineer pleaded guilty after allegedly trying to extort their employer by locking administrators out of Windows systems at scale.
Key Takeaways
Type of incident: Insider/extortion attempt that looks like “internal ransomware-style” disruption (account lockouts + operational sabotage).
Primary technique: Abused Windows admin access and domain controller scheduled tasks to delete domain admin accounts and mass-reset passwords.
Potential blast radius: Actions were intended to affect ~3,284 workstations and 254 servers, plus many domain/user accounts.
Extortion component: Sent coworkers a ransom email demanding 20 BTC and threatened further shutdowns (e.g., “40 random servers daily”).
Defender lesson: Insider threats can be “low malware, high privilege”—monitor for mass password resets, admin account deletions, and unusual scheduled task creation on DCs.

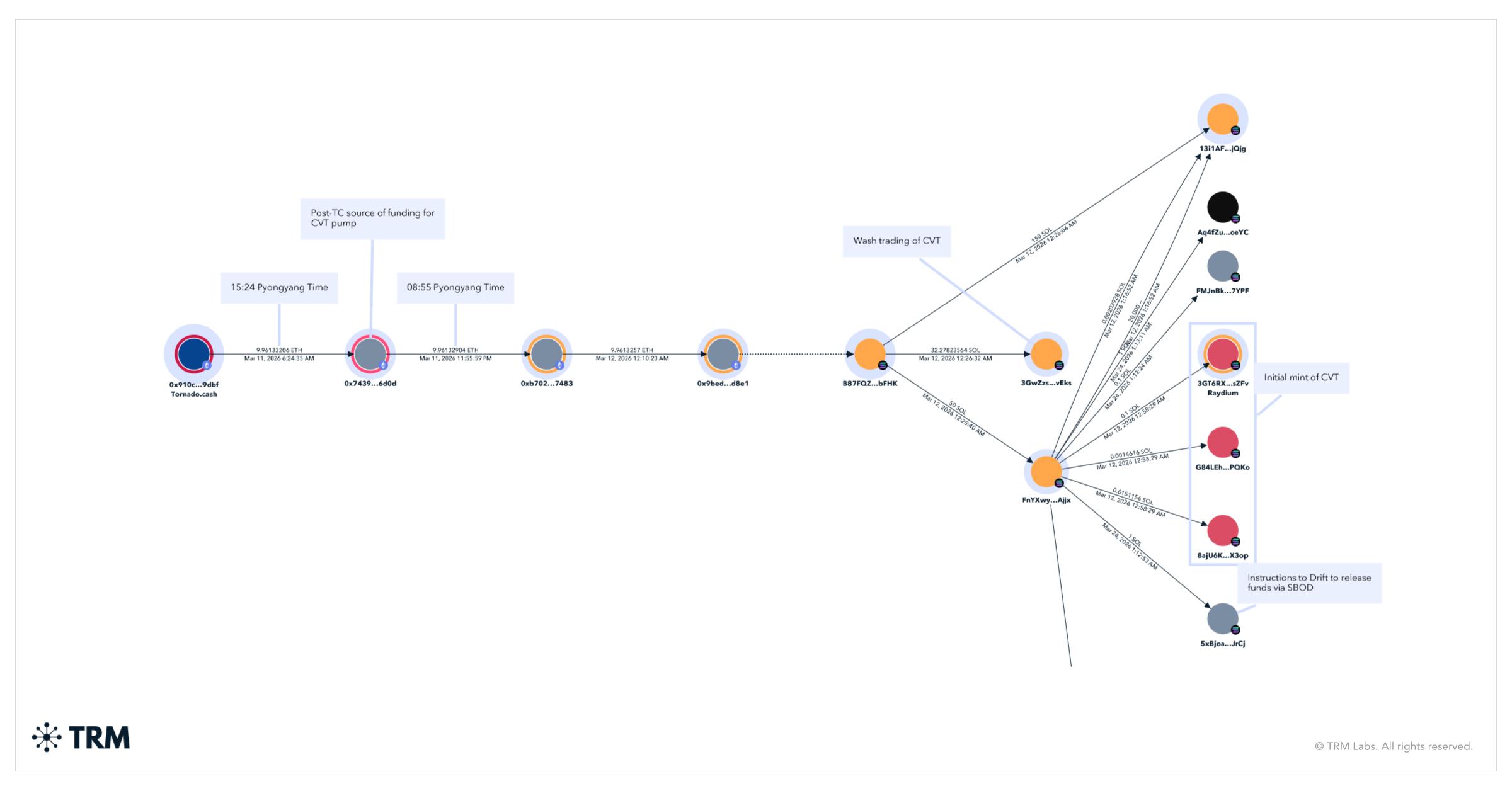
Drift Protocol Hit for $285M After Multisig Pre-Signing Abuse and Fake-Token Collateral
Attackers believed to be North Korea–linked drained about $285M from Drift Protocol (a major Solana perpetual futures exchange) in a rapid hit (~12 minutes), then quickly bridged most stolen funds to Ethereum
Key Takeaways
Impact: ~$285M stolen in minutes; funds bridged off-chain/cross-chain quickly.
Root cause: Process + governance failure, not a core “smart contract code bug.”
How they got control: Tricked multisig signers into pre-signing transactions with hidden permissions (using Solana durable nonce mechanics), then executed later.
What enabled speed: A zero-timelock Security Council migration removed the safety window to detect/stop malicious admin actions.
- Key trick: Created a fake collateral token (CarbonVote / CVT) and manipulated its “legitimacy” so oracles treated it as valuable collateral, enabling withdrawals of real assets.
Qilin Adds Die Linke to Leak Site Following “Serious” Cyberattack
A Russia-speaking ransomware group Qilin claimed it hacked Germany’s democratic socialist party Die Linke and is threatening to leak stolen data on its dark web site if a ransom isn’t paid.
Key Takeaways
Actor: Qilin ransomware group (active since 2022; has targeted organization across multiple regions/sectors).
Victim: German political party Die Linke.
Threat: Data leak extortion—publish stolen data unless ransom is paid.
Potential exposure: Internal org data + HQ employee personal info; membership DB reportedly not impacted.
Response actions: Systems partially taken offline; criminal complaint filed.
Context: German parties have been repeatedly targeted; past incidents include CDU, and SPD breach previously tied to APT28.

Storm-1175 Runs High-Tempo Medusa Ransomware Campaigns Exploiting Web-Facing N-Days
Storm-1175 (Microsoft’s name for a financially motivated actor) is running fast-moving Medusa ransomware operations by quickly exploiting recently disclosed vulnerabilities on internet-facing systems during the gap between disclosure and patching.
Key Takeaways
Big theme: Storm-1175 weaponizes N-day vulnerability (and occasionally 0-days) against web-facing perimeter apps before organizations patch.
Speed to impact: Initial access → exfiltration → Medusa ransomware often within days, sometimes <24 hours.
Initial access method: Exploits exposed, unpatched systems.
Post-compromise playbook: Webshell/remote access payload → create new admin users → lateral movement → credential theft → security tampering → ransomware deployment.
Common tools/techniques: Heavy use of LOLBins (PowerShell/PsExec), Cloudflare tunnels, and legitimate RMM tools (e.g., AnyDesk, ScreenConnect, SimpleHelp, etc.) for persistence/lateral movement; credential dumping (LSASS/NTDS.dit) and “double extortion” style exfil (e.g., Rclone).
Defender priorities:
- Patch/mitigate internet-facing apps immediately after disclosure; know what’s exposed externally.
- Watch for early signals: New admin account creation, RMM installs, Cloudflare tunnel binaries, LSASS/NTDS access, and attempts to disable/tamper with Defender/AV.

Claude Mythos: Powerful Bug-Finding AI Kept Limited to Reduce Cyber Misuse
Anthropic announced a new Claude model variant called Mythos that’s notably strong at finding software vulnerabilities/bugs.
Key Takeaways
What it is: A more advanced Claude model (“Mythos”) with improved code + reasoning, translating into stronger bug/vuln discovery.
Why Anthropic is limiting it: Concern that hackers could use it to improve/scale cyberattacks by finding exploitable weaknesses faster.
Capability example: Anthropic said Mythos Preview found a 27-year-old bug in OpenBSD.
Important nuance: Anthropic described it as general-purpose, not explicitly trained “for cybersecurity,” with cyber strength emerging from overall coding/reasoning gains.
Why this matters for defenders: Expect the disclosure-to-exploit window to shrink as models like this improve; patch speed and external attack surface management become even more critical.

APT28 Compromises Home Routers, Redirects DNS to Steal Microsoft 365 Credentials
APT28 (Fancy Bear / “Forest Blizzard”) is compromising SOHO/home-office routers to perform router-level DNS hijacking, letting them silently redirect victims’ legitimate Microsoft 365/OWA login traffic to attacker-controlled infrastructure and steal credentials.
Key Takeaways
Core technique: Compromise home routers → change DNS settings → redirect M365/OWA logins to attacker servers (often with convincing pages/certs) → steal credentials/tokens.
Why it’s dangerous: It operates below the endpoint/app layer, so many endpoint security tools won’t see the manipulation; every device on that network inherits the malicious DNS settings.
Initial access themes: Use of default credentials (example: Ubiquiti EdgeRouter defaults) and leveraging existing botnet infrastructure.
What gets stolen: Passwords, auth tokens, and NTLM-related material, enabling follow-on access to Microsoft 365.
Persistence note: A simple reboot isn’t enough—guidance calls for a full factory reset + firmware update + credential changes to remediate compromised routers.
Defensive focus: Identify remote-worker routers in use, remove default creds, patch firmware, restrict WAN management, and baseline/verify DNS settings; review M365 sign-in logs for unusual patterns.

CISA Warns: Internet-Facing PLCs Under Active Exploitation by Iranian-Associated Actors
Iranian-affiliated APT actors are actively exploiting internet-facing operational technology (OT) devices, especially Rockwell Automation/Allen‑Bradley programmable logic controllers (PLCs), across multiple US critical infrastructure sectors.
Key Takeaways
Who/what: Iranian-affiliated APT activity targeting internet-exposed PLCs (Rockwell/Allen‑Bradley noted; others may be at risk too).
Where: Multiple US critical infrastructure sectors, including Government services/facilities, Water & Wastewater, and Energy.
Impact: Attackers can extract PLC project files and manipulate HMI/SCADA display data, causing operational disruption.
How they access: Remote access to internet-facing OT devices using overseas infrastructure; CISA highlights suspicious traffic to common OT ports like 44818, 2222, 102, 502 and 22.
Immediate defensive action: Remove PLCs from direct internet exposure (use secure gateways/jump hosts + firewall), and hunt in logs for the provided IOCs and suspicious traffic on OT ports.
Rockwell-specific quick hardening: CISA notes setting the controller’s physical mode switch to RUN (per guidance) and following Rockwell’s hardening recommendations.

Northern Ireland Education Network Disrupted by Cyberattack; Officials Say No Data Compromised
A cyberattack disrupted Northern Ireland’s C2K education network, impacting IT services used by most primary and secondary schools.
Key Takeaways
What was hit: The C2K network (core IT network for NI schools) was disrupted.
Impact: Widespread service disruption across school IT systems (teaching/admin functions relying on C2K).
Data exposure: EA stated no data compromise at the time of reporting.
Response: EA contained the incident early and is working to fully restore and secure services, with extra focus on post-primary schools due to exams.
Bigger lesson: Education networks are high-impact targets—continuity planning + rapid containment are critical when core shared services go down.
In-the-Wild Exploitation of Flowise RCE Vulnerability CVE-2025-59528
A critical Flowise remote code execution (RCE) flaw (CVE-2025-59528) is now being actively exploited.
Key Takeaways
What: CVE-2025-59528 is a (critical / max severity) enables arbitrary code execution in Flowise.
Where it lives: The CustomMCP node, which unsafely evaluates user-supplied mcpServerConfig JavaScript (insufficient validation).
Status: Active exploitation observed (VulnCheck Canary network detected first-time exploitation).
Exposure: Researchers estimate ~12k–15k public Flowise instances, creating a large attack surface.
Patch guidance: Fixed in Flowise 3.0.6; upgrade to 3.1.1 (or at minimum 3.0.6).
Extra risk: The article also mentions other Flowise CVEs (CVE-2025-8943, CVE-2025-26319) seeing exploitation, suggesting broader attacker focus on Flowise deployments.
Immediate hardening: If Flowise doesn’t need to be public, remove it from the internet (restrict access) to cut risk quickly.

CIA Raises Profile of Cyber Espionage Division Amid Push for More Aggressive Cyber Posture
The CIA quietly upgraded its Center for Cyber Intelligence (CCI)—the agency’s elite cyber espionage organization—from being part of the Directorate of Digital Innovation to a full “mission center” as part of an internal reorganization ordered by Director John Ratcliffe.
Key Takeaways
What changed: CIA’s Center for Cyber Intelligence was promoted to a mission center (a higher-status org structure).
Why it matters: Mission-center status generally means more funding/resources and influence—“a bigger player at the table.”
Operational implication: CCI leadership now reports directly to the CIA director, signaling cyber as a top strategic priority.
Broader posture shift: The move aligns with a more combative U.S. cyber posture (explicitly calling for use of defensive + offensive cyber operations).
Context: CCI is the CIA’s cyber mission manager (analysis , operations , and espionage tooling). Its capabilities were publicly exposed in part by the 2017 Vault 7 leak.
Journalists Targeted in MENA by Bitter-Linked Hack-for-Hire Group
A “hack-for-hire” surveillance campaign—linked by researchers to infrastructure associated with the Bitter threat cluster—targeted journalists, activists, and government officials across the Middle East and North Africa.
Key Takeaways
How they attacked: Repeated credential phishing impersonating Apple Support and other trusted brands via iMessage/WhatsApp, plus LinkedIn sock‑puppet outreach and link-shorteners to drive victims to malicious pages.
Notable technique: OAuth “consent phishing” against Google accounts—abusing legitimate Google OAuth flows to trick targets into granting access to an attacker-controlled app (instead of only using fake login pages).
Malware angle: Some infrastructure overlapped with Android spyware delivery lures; reporting ties parts of it to ProSpy/ToSpy style fake “encryption plugin” sites (Signal/Telegram lookalikes).
Attribution note: Lookout linked the activity to a hack-for-hire operation with ties to Bitter, but said it’s unclear if this is Bitter expanding targeting or a separate group with infrastructure overlap.
Practical defense takeaway: For high-risk users/organizations, treat messaging-app links + OAuth consent prompts as high-risk; enforce phishing-resistant MFA where possible and monitor for new devices/apps added to Apple/Google accounts.

Minnesota Deploys National Guard Cyber Team After Winona County Ransomware Attack
Winona County, Minnesota detected a ransomware attack that disrupted county computer systems and digital services. In response, Gov. Tim Walz deployed the Minnesota National Guard’s cybersecurity team to help the county investigate, recover faster, and harden systems.
Key Takeaways
Incident: Winona County hit by ransomware, causing disruption to critical systems/digital services.
Response: County took affected systems offline; residents should expect delays; emergency services still running.
Support: Minnesota National Guard sent ~15 cybersecurity experts to assist recovery and deeper investigation.
Repeat targeting: This was the second cyberattack on Winona County in 2026 (first in January), and officials said it’s likely not the same group.
Bigger lesson: Local governments are resource-constrained but high-impact, making them attractive ransomware targets—state-level surge support can speed containment and resilience improvements.
Hardcoded Google API Keys in Android Apps Reveal Gemini AI Access Paths
A CloudSEK report says a change/behavior in Google’s API key model can unintentionally grant existing “public” Google API keys (often embedded in Android apps) access to Gemini AI endpoints once Gemini is enabled in a Google Cloud project.
Key Takeaways
Core issue: If a Google Cloud project enables the Gemini API, existing API keys may silently gain access to Gemini endpoints without explicit re-scoping/consent.
Why this is dangerous: Keys that developers previously believed were “safe” to embed client-side (Maps/Firebase-style keys) may now unlock AI capabilities/data paths they weren’t intended to.
Scale: CloudSEK analyzed 10,000 Android apps, finding 32 active keys across 22 apps, with the apps totaling 500M+ installs.
Proof-of-impact example: Researchers said they could access user-uploaded audio files from an English-learning app via the Gemini Files API (metadata, timestamps, and accessible links).
Primary risks:
- Access to private files/data reachable via Gemini APIs
- Unexpected cloud bills from unauthorized API usage
- Service disruption via quota exhaustion / abuse
Real-world cost signal: The article cites incidents where compromised keys led to rapid charges (examples: $15.4k in hours, and $128k losses).
Recommended actions: Audit cloud projects and keys, rotate exposed keys, and restrict keys so they can only call required APIs (don’t leave broad access enabled).

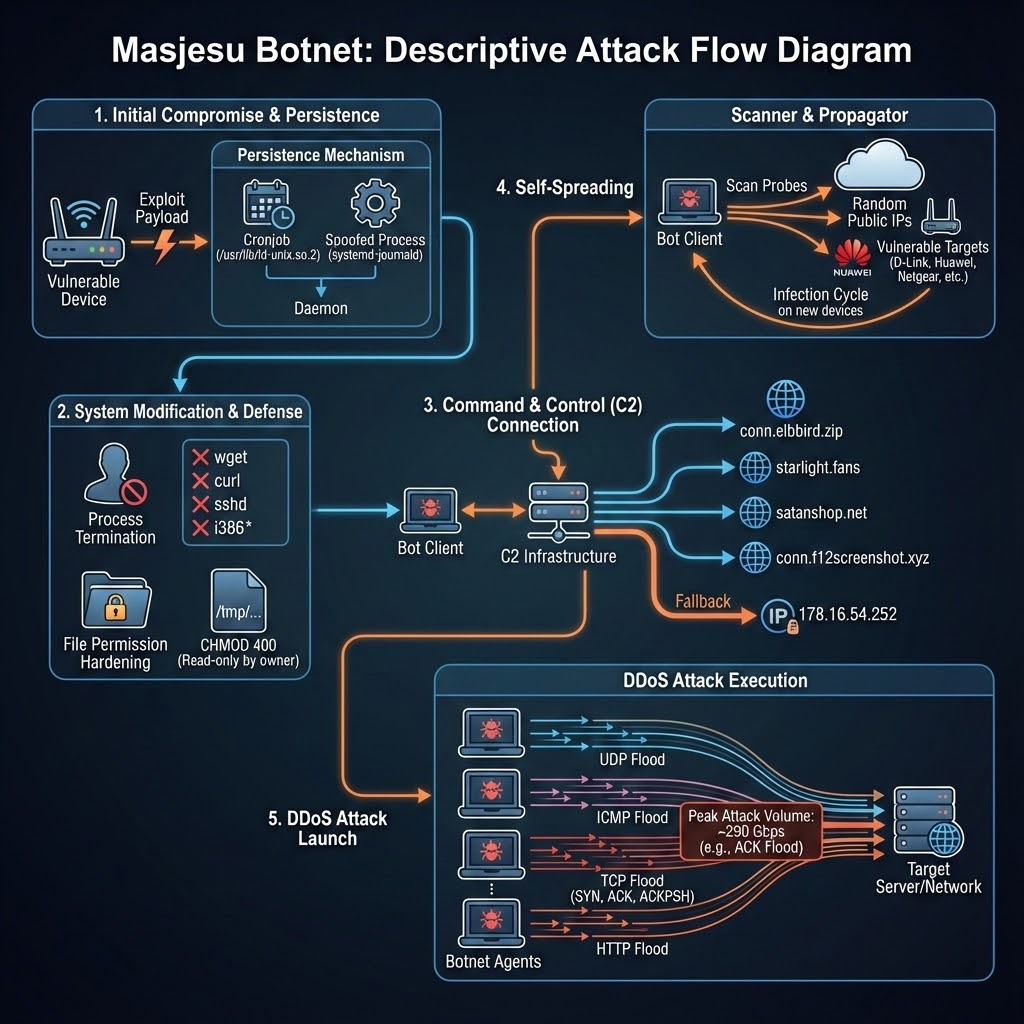
Masjesu: Stealth DDoS-for-Hire Botnet Exploits Routers and Gateways Across Architectures
Masjesu is an IoT-focused botnet (active since ~2023) that’s being marketed as a DDoS-for-hire service, with an emphasis on stealth and long-term persistence rather than loud, mass infections.
Key Takeaways
What it is: Masjesu (aka “XorBot”) = commercially run DDoS-for-hire IoT botnet advertised on Telegram.
Primary target: Internet-exposed IoT devices (routers/gateways/embedded systems) across many architectures (MIPS/ARM/x86/etc.).
Key differentiator: Evasion-by-design — it avoids “high-profile” IP ranges (e.g., DoD) to stay under the radar and survive longer.
How it spreads: Scans random IPs and exploits known weaknesses in devices from vendors like D-Link, GPON, Netgear (and others mentioned in the report).
How it hides/persists: XOR-encrypts strings/configs; renames itself to look legitimate; installs a cron job (every ~15 minutes).
What it does: Executes TCP, UDP, and HTTP flood attacks; reported attacks up to ~290 Gbps.
Defender lesson: This is a “quiet” IoT botnet—don’t rely on noisy scanning signatures alone; prioritize patching/exposure reduction for edge devices and monitoring for bot-like persistence behaviors (cron + masquerading).
New Chaos Variant Exploits Cloud Misconfigs, Expands Beyond Routers and Edge Devices
A new Chaos malware variant (an evolution tied to the Kaiji botnet lineage) is now being observed exploiting misconfigurationed cloud deployments—expanding beyond the more typical focus on routers/edge devices.
Key Takeaways
What changed: Chaos is shifting from primarily edge/IoT-style targeting to misconfiguration cloud workloads (cloud misconfig exploitation).
How initial access happens (observed): An HTTP request with embedded shell commands was used to download/execute the Chaos binary (seen on a misconfigured Hadoop honeypot).
Capabilities: Remote command execution, propagation, crypto-mining, and DDoS remain core features.
New capability: Adds a SOCKS proxy, letting attackers route traffic through victims (stealth + resale/monetization).
Attribution signal (not confirmed): Darktrace linked the command server domain to infrastructure previously used by Silver Fox (reported as context, not definitive attribution).
Defender takeaway: Cloud misconfigurations are now a direct botnet entry point—hardening exposed services and limiting unauthenticated command execution paths is critical.