Threat Newsletter March 2, 2026

This week’s threat intel shows attackers using AI to scale malware and intrusions, with credential theft and internet-exposed systems as common entry points. Priority actions are to lock down management interfaces, enforce MFA, rotate secrets, and urgently patch actively exploited bugs (notably Roundcube and Cisco SD-WAN).
Arkanix Stealer: Multi-Platform Credential Theft at Scale
Kaspersky researchers say an information-stealing malware operation named "Akranix Stealer"—which appeared in dark web forums in October 2025—was likely developed as an AI-assisted experiment.
Key Takeaways
🪲 Malware: Arkanix is a Malware-as-a-Service (MaaS) info stealer sold on criminal forums, with web panel for managing victims and payloads.
📩Distribution: Likely spread via phishing/lures, based on loader filenames.
💡Primary Goal: The goal for the malware is credential and session theft, especially from browsers (passwords, cookies, auto fill, history, OAuth2 tokens) with a heavy focus on banking and crypto targets. In addition, it also targets popular apps and accounts such as:
- Telegram session data.
- Discord credentilas and self-spreading via DMs.
- VPN clients ( Mullvad, NordVPN, ExpressVPN, ProtonVPN).
🪲Variants: It has both a Python and C++ versions. The C++ version includes stronger evasion, including sandbox/debugger checks and patching AMSI/ETW to reduce detection and telemetry.
💡Notable Trend: Kapersky highlights signs of AI-assisted (LLM-assisted) development, implying lower barriers and faster malware iteration.
🛡️Mitigation: In order to protect against this organizations must:
- Reduce infostealer impact by enforcing phishing-resistant MFA, limiting saved browser credentials, and hardening endpoints with EDR plus least privilege.
- Strengthen email and web controls to reduce phishing and trojanized “checker” lures, and monitor for unusual access to browser stores, Telegram/Discord data, VPN credential files, and bulk file-zipping and exfiltration.
No Zero-Day Needed: AI-Scaled FortiGate Takeovers via Weak Passwords
Amazon says a Russian-speaking threat actor used generative AI as a force multiplier to compromise 600+ internet-exposed FortiGate management interfaces across 55 countries.
Key Takeaways
🔒No Exploit required: Access was gained by attacking exposed FortGate management ports and brute-forcing common passwords where MFA was not enabled.
⚠️Configs were the prize: Once in, the actor pulled FortiGate configuration backups containing admin creds, SSL-VPN creds, routing and topology, policies, and other network details.
💡Post-compromise automation: Custom GO and Python tooling and scanners were used for network classification, port scanning, identifying DCs/SMB, and HTTP discovery.
🔧AI amplified a lower-skill operator: Amazon describes the attacker as low-to-medium skill, but using LLMs to generate attack steps, write scripts, plan lateral movement, and create recon frameworks.
🛡️Mitigation: Do not expose management interfaces to the internet, require MFA, avoid reusing VPN and AD passwords, and harden backup infrastructure.

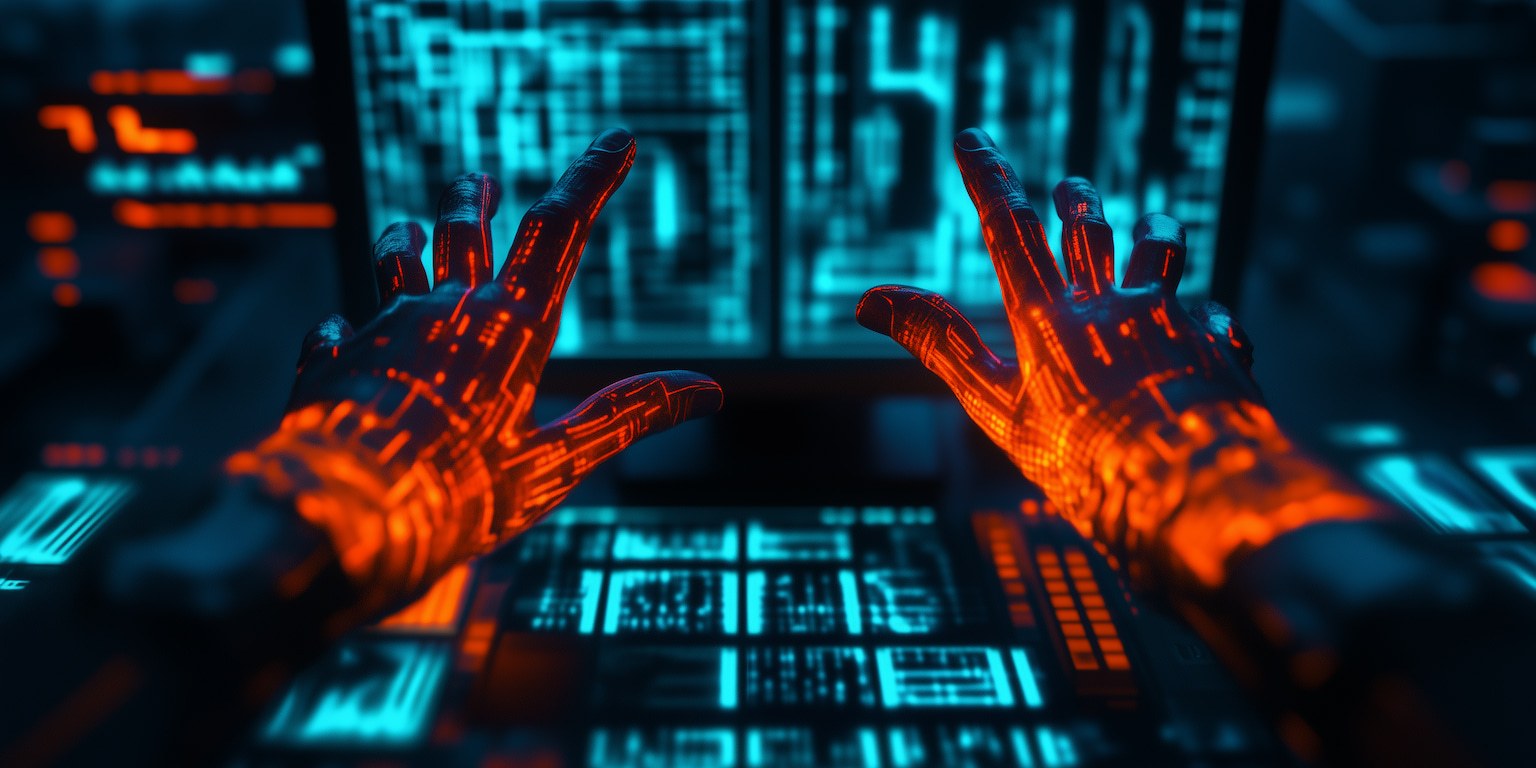
Claude Code Security Launches in Preview to Boost DevSecOps Vulnerability Discovery
Anthropic is rolling out Claude Code Security, a new feature for Claude Code that scans software codebases for vulnerabilities and recommends patches for human review.
Key Takeaways
❗What it is: This is a new feature for Claude code that does AI-assisted vulnerability scanning plus patch recommendations, with a human -in-the-loop approval step.
💡Who gets it: Limited research preview for Enterprise and Team customers.
⚠️Why it matters: Designed to counter AI-enabled vulnerability discovery by giving defenders faster identification and remediation issues.
💡How is it different from basic scanners: Goes beyond static pattern matching by reasoning across components, tracing data flows, and flagging issues rule-based tools may miss.
🔍 Noise Reduction: Findings go through a multi-stage verification to reduce false positives, and include severity and confidence ratings.
Compromised Websites as Delivery Infrastructure: ClickFix Chain Ends in MIMICRAT RAT
Elastic Security Labs reports an active ClickFix campaign using compromised legitimate websites to deliver a five-stage infection chain ending in MIMICRAT.
Key Takeaways
❗Legit Sites were the delivery Infrastructure: Attackers compromised trusted websites and injected malicious JavaScript to start the chain.
🔍ClickFix social engineering is the entry point: Victims are tricked into running a copied PowerShell command, which kicks off the staged download/execution flow.
🔍 Strong defensive evasion early: The PowerShell stages include ETW patching and AMSI bypass, reducing visibility before payload delivery.
🔧 Multi-stage execution flow: The execution delivery of the RAT is within memory. A Lua loader decrypts/decodes and executes shell-code, leading to the final RAT with minimal on-disk artifacts.
🪲MIMICRAT: This is a custom RAT that has native implant with malleable C2 profiles, token impersonation, theft, and SOCK5 proxy/tunneling.
🌐 Campaign is active and broadly targeted: Elastic notes multiple industries/geographies and localization across many languages, suggesting opportunistic scale.

Wynn Resorts Breach: ShinyHunters Extortion Exposes 800K Employee Records
UpGuard reports that Wynn Resorts confirmed a breach tied to ShinyHunters. Attackers accessed systems in September 2025 and stole roughly 800,000 employee records.
Key Takeaways
🚨 Threat Actor: ShinyHunters is attributed as the extortion actor behind the Wynn Resorts breach.
🌐 Scale: 800K employee records exposed, including SSNs and DOBs.
🔍 Likely Root Cause: UpGuard states the incident originated via a vulnerability in Oracle PeopleSoft.
❗ Impact: The breach elevated the risk of targeting phishing, account fraud, and long-term identity theft for affected employees.
💡Response: Wynn activated incident response and is offering credit monitoring to impacted employees.

SANDWORM_MODE: Shai-Hulud-Style npm Worm Adds CI Propagation and AI Toolchain Injection
An active supply-chain campaign dubbed SANDWORM_MODE (Shai-Hulud-like) uses at least 19 malicious npm packages to steal credentials and crypto keys, then propagates by abusing stolen npm and GitHub identities.
Key Takeaway
🪲 Supply-chain worm via npm: At least 19 malicious packages attributed to publisher aliases (offical334) and (javaorg).
⚠️ Steals high-value secrets: Grabs CI/CD secrets, API tokens, and cryptocurrency keys, plus broader developer environment data.
🚨Propagates through GitHub and npm: The malware uses stolen tokens to spread and also drops a weaponized GitHub Action to harvest CI secrets.
🔍Standout Feature: The malware has a AI tool-chain targeting where the it can deploy a malicious MCP server to prompt-inject and harvest sensitive files and LLM API keys from popular AI coding assistants.
🕵️Potential destructive behavior: Includes a kill-switch style home directory wipe if it loses access to GitHub or npm.
🛡️Defense: Remove the listed packages from the report, rotate npm/GitHub/CI secrets, and review package.json, lockfiles, and .github/workflows.

Actively Exploited Roundcube Bugs Added to CISA KEV — Urgent Patching Required
CISA added two Roundcube webmail vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation in the wild.
Key Takeaways
🚨Actively Exploited : CISA says they Roundcube flaws are being used in real attacks.
Key CVEs:
- CVE-2025-49113 (CVSS 9.9): authenticated RCE via unsafe deserialization tied to an unvalidated
_fromparameter (fixed June 2025). - CVE-2025-68461 (CVSS 7.2): XSS via an
animatetag in an SVG document (fixed December 2025).
⚠️ Exploit Speed: The RCE was reportedly weaponized quickly after disclosure and even marketed for sale shortly after.
🛡️ Action: Patch and upgrade Roundcube to versions containing the fixes and validate exposure, especially if webmail is internet-facing.

Python Malware Behind Unauthorized PayPal Transfers Uses Disposable C2 and Commercial Tools
A fraud investigation into unauthorized PayPal transfers uncovered a multi-stage malware intrusion using hidden PowerShell execution, staged downloads, and a concealed Python environment.
Key Takeaways:
🔍 User-visible clue: Brief “black windows” appeared , and screenshots exposed fragments of a command script involved in decoding and executing payloads.
❓Initial Entry unclear: Investigators could not confirm the initial vector, but suggest likely routes like social enigneering, malicious downloads, or email-based delivery.
🔧 PowerShell-driven infection chain: Repeated hidden PowerShell with execution policy bypass downloaded a fake svchoss.exe a fake svchoss.exe (masquerading as svchost) from 43.156.63[.]124 .
🥷Persistence established: Additional batch and VB scripts were dropped into startup folders to survive reboots.
💡Python malware staged on host: Memory analysis identified a concealed Python environment under %LOCALAPPDATA%\\Microsoft\\SystemCache25 and artifacts like python.exe, xro.py, and encoded binaries.

INC Ransomware Claims 208GB Theft as Air Côte d’Ivoire Activates Continuity Plans
Air Côte d’Ivoire confirmed it suffered a cyberattack on February 8, 2026, after the INC ransomware group claimed it stole 208 GB of data from the airline.
Key Takeaways
⚠️ Confirmed incident: Air Côte d’Ivoire acknowledges a cyberattack affecting parts of its information systems
❗Ransomware Claim: INC ransomware claims it stole 208 GB and set a ransom deadline of February 24.
🌐 Operational Impact: The airline brought in technical teams an invoked continuity plans to keep flight running.
💡Data-leak risk acknowledged: The airline warned of potential risks to service providers, passengers, and employees, but said flight operations remain stable.
Step Finance Shuts Down After $40M Treasury Theft
Step Finance, a Solana DeFi platform, announced it is shutting down after roughly $40 million was stolen from its treasury on January 31. The company said the theft occurred after executive team devices were compromised.
Key Takeaways
🚨 VWhat happened: $40M treasury theft drove the shutdown of Step Finance.
🔍 Limited Recovery: Step Finance said it recovered about $3.7M in stolen Remora assets and about $1M in other coins.

UK Regulator Hits Reddit With £14M Fine for Inadequate Age Verification
The UK data protection regulator (ICO) fined Reddit £14.47m for unlawfully processing children's personal data and failing to implement effective age assurance, potentially exposing children to harmful content.
Key Takeaways
❗Fine amount and reason: Reddit fined £14.47m for child data protection and age-check failings.
🔍 Core issues: The ICO says Reddit did not have effective age assurance, and under-13 data was processed without a lawful basis.
🌐 Regulatory Pressure is increasing: ICO and Ofcom actions signal a push toward stronger age assurance for services likely used by children.
💡Reddit response: Reddit says it is committed to privacy, intends to appeal, and disputes the need to collect more identity data.

Medusa RaaS Meets Lazarus: North Korea Tied to U.S. Healthcare Ransomware Wave
North Korean state-sponsored hackers associated with the Lazarus Group are using Medusa ransomware in attacks against U.S. healthcare organizations and non-profits, based on a joint investigation by Symantec and the Carbon Black Threat Hunter Team.
Key Takeaways
🕵️Actor: Activity attributed to Lazarus Group ( North Korea’s RGB-linked umbrella of threat actors.
🪲Ransomware used: Medusa RaaS, believed to be run by a cybercrime group called Spearwing, with affiliates carrying out intrusions for a cut of ransoms.
🎯 Victim focus: U.S. healthcare organizations and non-profits, including a mental health services provider and an educational facility for autistic children.
🌐 Scale and timing: In the report, they note four U.S attacks since Nov 2025, plus an identified attack on a Middle East target.
📈 Pattern: Medusa uses double extortion and may auction stolen data if ransoms are not paid.
💡Related Lazarus subgroup context: The researchers also reference Stonefly (also known as Andariel) as a Lazarus subgroup believed to be involved in similar activity.

Google Takes Down UNC2814 Infrastructure Behind GRIDTIDE Espionage Campaign
Google says it worked with partners to disrupt the infrastructure of a suspected China-linked cyber espionage group tracked as UNC2814. The group is tied to 53 breaches across 42 countries, with suspected activity in over 70 countries.
Key Takeaways
🎯 Campaign: The campaign is associated with a backdoor called GRIDTIDE that abuses Google Sheets API for command-and-control, helping the traffic blend as legitimate SaaS activity.
🌐 Scale: At least 53 organizations breached across 42 countries; many compromises may have persisted for years.
🔍 Tradecraft: Uses SaaS APIs for C2, specifically Google Sheets via the GRIDTIDE backdoor.
🪲 GRIDTIDE capabilities: This is a C-based backdoor that supports file upload/download and arbitrary command execution.
💡Intrusion activity noted: The threat actor performed Lateral movement via SSH, plus living-off-the-land activity, persistence via a systemd service (/etc/systemd/system/xapt.service) spawning from /usr/sbin/xapt, and use of SoftEther VPN Bridge.
🛡️ Disruption actions: Google says it terminated attacker-controlled Google Cloud projects, disabled known infrastructure, and cut off access to attacker-controlled accounts and Sheets API calls used for C2; it also issued victim notifications
💡Big picture: Reinforces that internet-facing web servers and edge systems remain common entry points for long-term espionage operations

CISA Emergency Directive Issued After Cisco SD-WAN Auth Bypass Exploitation
Cisco disclosed a critical authentication bypass in Cisco Catalyst SD-WAN that has been actively exploited as a zero-day since at least 2023.
Key Takeaways
🛠️ Vulnerability: The bug (CVE-2026-20127) lets an attacker authenticate to affected SD-WAN control components and potentially insert a rogue peer into the SD-WAN fabric, enabling follow-on network compromise.
❗What it affects: Cisco Catalyst SD-WAN controller (vSmart) and SD-WAN Manager (vManage), including on-prem and SD-WAN Cloud deployments.
🕵️ Threat Activity: Cisco Talos tracks the exploitation as UAT-8616 and reports activity going back to 2023. The actor may have chained this with CVE-2022-20775 (via downgrade/restore behavior) to achieve root while reducing detection chances.
⚠️ Government Urgency: CISA issues Emergency Directive as the exploitation poses an imminent threat to federal networks and that devices must be patched by 5:00 PM ET on February 27, 2026.
🛡️ Mitigation: Cisco says updates are required and no workaround fully mitigates the issue. Management interfaces should not be exposed to the internet.