Threat Newsletter February, 9 2026

Welcome to this week’s Threat Intelligence Newsletter. This edition focuses on high-impact vulnerabilities and active tradecraft that shorten the path from initial access to full compromise, including multiple remote code execution (RCE) scenarios with low user interaction, and a notable software supply chain incident.
We cover a one-click RCE in OpenClaw (CVE-2026-25253) that abuses token trust and cross-site WebSocket behavior, and a critical pre-auth RCE in BeyondTrust RS/PRA (CVE-2026-1731) with clear patch guidance for SaaS and self-hosted environments. We also highlight APT28 activity exploiting a Microsoft Office security feature bypass (CVE-2026-21509), where weaponized documents enable execution without macros and support stealthy persistence. Finally, we review a Notepad++ update infrastructure compromise, reinforcing the need to treat trusted update channels as a prime adversary target.
Across these items, the theme is consistent: reduce exposure quickly (patch and harden), restrict common execution paths, and monitor for the specific behaviors adversaries rely on to establish persistence and disable defenses.
One-Click RCE in OpenClaw: AI assistant Vulnerability (CVE-2026-25253)
A high-severity vulnerability in OpenClaw (formerly referenced as Clawbot/Moltbot) allowed one-click remote code execution via a crafted malicious link. The vulnerability stems from the Control UI trusting a gatewayURL query-string parameter and auto-connecting on page load, which leaks a stored gateway token to the attacker's controlled server. This exploit enables cross-site WebSocket hijacking, allowing attackers to bypass security sandboxes and execute arbitrary commands on another machine.
Key Takeaways
🔒Impact: One-click path to full gateway compromise and RCE by stealing a gateway auth token and abusing privileged scopes.
👊 Attack precondition: The user must have authenticated to the Control UI (so a usable token exists to steal).
⏰ Root Causes: The root causes are two design failures on OpenClaw:
- Trusting the gatewayURL from the query string and auto-connecting.
- Missing WebSocket Origin validation, enabling across-site WebSocket hijacking.
🛡️Mitigations: Ensure OpenClaw is updated to version 2026.1.29 or later.
0-Day BeyondTrust RCE Vulnerability
Key Takeaways
BeyondTrust disclosed a critical pre-authentication remote code execution (RCE) vulnerability affecting Remote Support (RS) and Privileged Remote Access (PRA) products. Tracked as CVE-2026-1731, this command injection flaw allows an unauthenticated attacker to send crafted requests that execute arbitrary OS commands without any user interaction.
👊Attack: This is a OS command injection vulnerability that allows an unauthenticated attacker to send crafted requests that execute arbitrary OS commands without any user interaction.
📈Impact: Successful exploitation could lead to complete system compromise, enabling attackers to gain unauthorized access to sensitive data, exfiltrate confidential information, disrupt critical services, and potentially pivot to other systems within the network.
🚧 Affected Versions: The versions that are affected by this vulnerability is BeyondTrust Remote support version 25.3.1 and earlier and Privileged Remote Access version 24.3.4 and earlier.
🛡️Mitigations: Organizations that are using the SaaS application were automatically patched on Feb 2, 2026. Self-hosted customers need to patch manually via the appliance interface:
- BT26-02-RS (Remote Support)
- BT26-02-PRA (Privileged Remote Access)
- If your organization is running Remote Support 21.3 or earlier, or Privileged Remote Access version 22.1 or earlier, you must first upgrade to a supported version. Remote Support users should upgrade to 25.3.2 for full protection.

APT28 (Fancy Bear) Exploit Microsoft Office (CVE-2026-21509)
Key Takeaways
Russian state threat actors (APT28) are exploiting a newly disclosed Microsoft Office security feature bypass (CVE-2026-21509) in a campaign dubbed Operation Neusploit. The campaign targets government entities in parts of Eastern Europe.
🔒Exploit Velocity: APT28 moved quickly, abusing CVE-2026-21509 soon after public disclosure.
🚨Low-friction execution: Weaponized documents can trigger execution without relying on macros, lowering user friction and improving success rates.
🕵️Espionage Focus: Payloads are geared toward collection and persistence, including Outlook mail theft (MiniDoor) and longer-term access via COVENANT Grunt.
🔏Sophisticated Stealth: Exploitation uses malicious Office documents (including RTF/ Word lures) to drop malware chains that branch into different espionage outcomes:
- One branch drops MiniDoor, an Outlook email staler that collects mail from folders like inbox/Junk/Drafts and forwards it to attacker-controlled addresses.
- Another branch delivers PixyNetLoader, which establishes persistence (including COM object hijacking) and executes later-stage payloads using stenography to hide malicious shell code in PNG files to deploy a COVENANT Grunt implant for C2 and post-exploitation activity.
🛡️Mitigations: Organizations should patch immediately as this is the most effective control to fight against this flaw.
- Block or constrain common staging techniques seen in the chain such as harden or restrict WebDAV usage.
- Block execution of downloaded shortcut files (LNK) from user-writable locations when possible.
- Use endpoint controls (ASR/EDR policies) to block Office apps from creating child processes and from launching script interpreters of LOLBins.
- Focus on telemetry on behaviors consistent with the described trade craft:
- Office Spawning unusable processes
- winword.exe
- rundll32.exe
- regsvr32.exe
- mshta.exe
- powershell.exe
- cmd.exe
- Suspicious COM persistence / COM object hijacking artifacts.
- Office Spawning unusable processes
Notepad++ Updates compromised in Supply Chain attack
Notepad++ developers disclosed a breach of their update infrastructure. Threat actors gained unauthorized access through a hosting provider-level incident between June and September 2025. This allowed them to maintain access and deliver targeted malware via malicious update components over several months.\
Key Takeaways
🎯 Target: The China-linked threat actor “Lotus Blossum” (APT31) used a trusted update path and used IP filtering to deliver malware to specific target within telecom and financial organizations, which can be harder to spot than large-scale outbreaks.
🌐 Chrysalis Backdoor installed: Targeted victims were infected with a backdoor capable of spawning shells, collecting files, and deploying Metasploit and Cobalt Strike for long-term persistence.
🛡️Proactive defenses: Treat software updaters as high-risk trust paths. Restrict which endpoints can run updaters and where updates can be fetched from.
- Use WDAC or EDR application control to prevent updaters from launching unexpected binaries.
- Monitor for suspicious or uncommon file-hosting services used for staging.

Critical RCE in React Native
A critical remote code execution flaw in React Native's Metro development server (CVE-2025-11953), nicknamed "MetroShell," is being actively exploited to compromise developer machines. Attackers can execute arbitrary OS commands by sending specially crafted HTTP requests.
Key Takeaways
🔒Improper input validation: The flaw stems from a improper input validation on the Metro server’s /open-url endpoint, which directly passes user controlled data to the unsafe open() function without sanitation.
💥 Impact: The vulnerability affects the widely used @react-native-community/cli versions 4.8.0 through 20.0.0-alpha.2. There are 2,500 Metro servers exposed on the public internet.
🎯 Target: Dev tooling is a high-value target. Compromising a developer workstation can yield source code, credentials, API keys, and paths into production environments.
🛡️ Mitigation: Organizations need to patch and harden devices immediately and do the following:
- Update to @react-native-community/cli 20.0.0+
- Ensure Metro binds only to localhost and is not reachable from untrusted networks.
- Monitor for suspicious Metro HTTP requests and developer endpoints being accessed remotely.

Increase in Python stealers targeting MacOS
Microsoft reports that infostealers are expanding beyond traditional Windows-focused campaigns. Thanks to Python's cross-platform capabilities, threat actors are increasingly targeting macOS—often via malvertising, fake installers, and "ClickFix" prompts—to steal browser secrets, keychain data, crypto wallets, and developer credentials.
Key Takeaways
💥 MacOs being targeted: Attackers are using Python’s flexibility to deploy infostealers such as DigitStealer, MacSync, and AMOS in their campaigns. These infostealers rely on native utilities such as AppleScript automation, and fileless-like execution to steal browser secrets.
🎯 Target: MacOS is a primary target now where attackers are using common lures such as fake software, DMGs, and ClickFix style prompts.
💎Targeting High value assets: Developer environments are high-value. The stealers target not just passwords and cookies, but also developer secrets (cloud credentials, SSH keys, and Kubernetes configs).
🛡️Monitoring: Organizations must monitor for unusual terminal activity, unauthorized iCloud Keychain access, and suspicious network egress to newly registered domains.
💡End-User Education: Train your end users on malvertising redirect chains to fake ClickFix prompts.

EnCase EDR Killer
Security researchers have uncovered a sophisticated "EDR killer" tool that uses the Bring Your Own Vulnerable Driver (BYOVD) technique. The tool abuses a legitimate—but long-revoked—EnCase kernel driver to disable endpoint security products. It targets 59 security processes and runs a kill loop every second to keep defenses down.
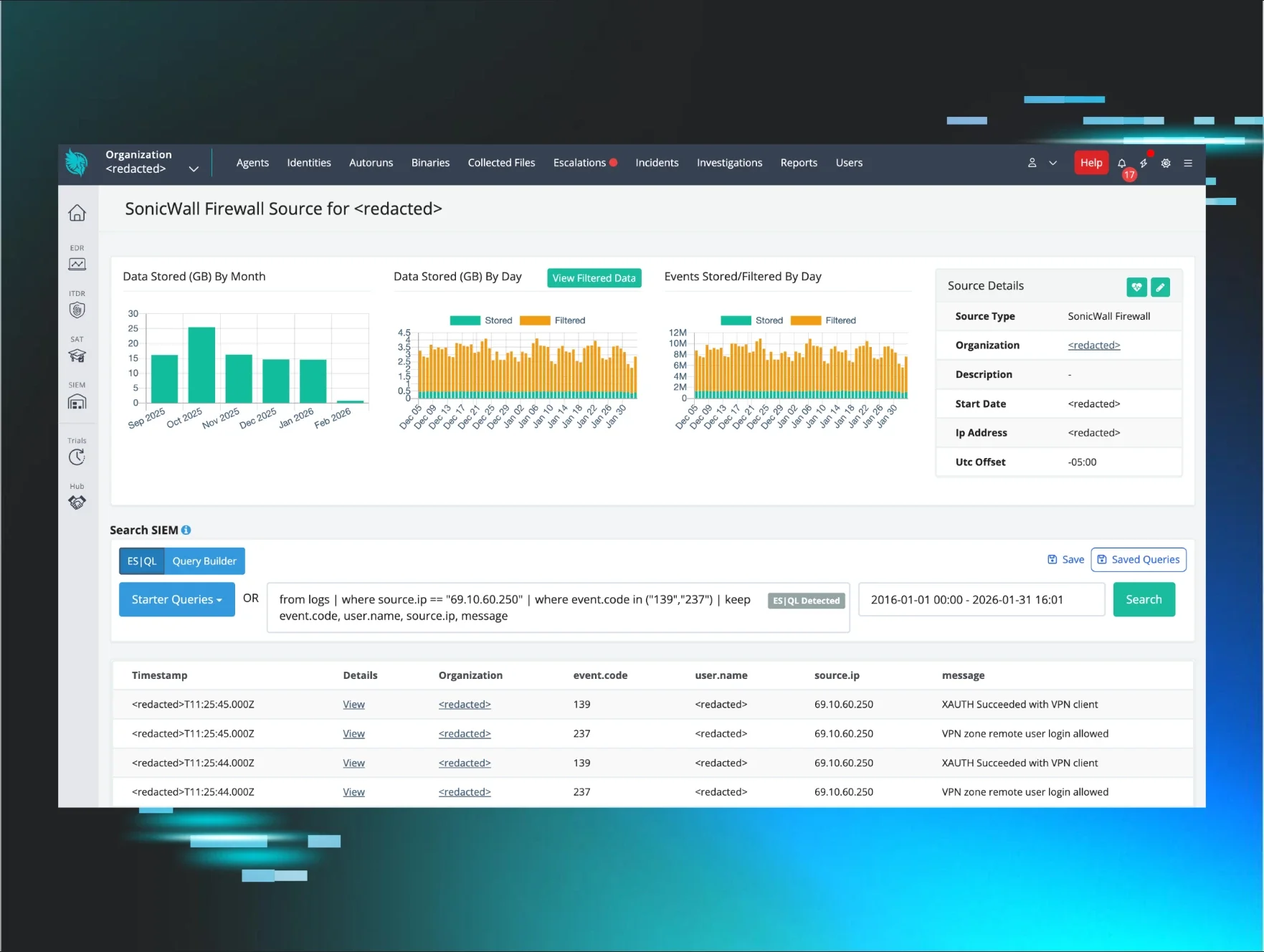
🔒Initial Access: The attackers got initial access via compromised SonicWall SSL VPN credentials where MFA was not enabled.
🔒Initial Access: The attackers got initial access via compromised SonicWall SSL VPN credentials where MFA was not enabled.
🔓 Flaw: Because Windows driver signature enforcement validates the signature chain and timestamp, it doesn’t check the certificate revocation lists (CRLs) during driver load.
🥷Persistence: The tool disguises itself as a legitimate “OEM hardware service” ensuring it remains active even after system reboots.
🛡️ Mitigation: Primary defensive actions are straightforward and high impact:
- Enable MFA on all remote access, especially VPN,
- Monitor VPN authentication logs for anomalies and suspicious recon patterns after login.
- Enable HVCI/Memory Integrity to enforce Microsoft vulnerable driver block list.
- Consider Windows Defender Application Contol (WDAC) to block abused vulnerable drivers.
- Create alerts on suspicious drivers being created.
Rasnomware groups abusing ISPsystems
Sophos reports that cyber criminals are abusing legitimate virtual machine provisioning infrastructure (ISPsystem's VMmanager platform) to supply large numbers of Windows VMs that appear repeatedly in malicious activity.
🚨 Evading detection: Legitimate infrastructure can provide “cover” at scale. Threat actors using Manger-provisioned VMs lets adversaries hide in a sea of normal hosting traffic and systems.
🌐 Bulletproof hosting remains a force multiplier: A small cluster of providers with reputational/sanctions baggage was cited as hosting a large portion of the observed malicious VMs, enabling persistence against abuse reports.
💡Proactive Detection: Security must treat their virtualization layer as a critical attack surface. Make sure software is patched and audit logs are reviewed for anomalies.