ShinySp1d3r Analysis

Overview
ShinySp1d3r is a newly observed Ransomware-as-a-Service (RaaS) operation linked to the continued evolution of the ShinyHunters ecosystem and its collaboration with Scattered Spider/COM. While ShinyHunters first emerged in 2020 as a high-volume data theft and extortion group, recent campaigns show a clear progression toward more sophisticated intrusion models that blend social engineering, credential abuse, and downstream impact operations. This shift reflects a broader trend in the threat landscape: identity-based access and SaaS compromise increasingly serve as the entry point for attacks that culminate in enterprise-wide disruption.
This report documents ShinySp1d3r from both an operational and technical perspective. It contextualizes the group’s activity across major campaigns, including large-scale compromises involving Snowflake customer environments and Salesforce-focused vishing tactics, and highlights the role of third-party integrations and stolen OAuth tokens in expanding attacker reach. It then presents technical findings from malware analysis of a Go-based Windows payload, including indicators of packing and signing abuse, host profiling and mutex creation logic, API hashing, privilege-related behavior, and Event Tracing for Windows (ETW) suppression through EtwEventWrite hooking.
Finally, this report outlines the encryptor’s functional characteristics and impact tradecraft, including process and service termination to unlock files, partial encryption for speed, and cryptographic implementation details (ChaCha20-based obfuscation combined with RSA-OAEP protection). The goal is to provide defenders and responders with a clear understanding of how ShinySp1d3r fits into the actor’s broader playbook, what makes the ransomware technically and operationally significant, and which behaviors and indicators are most actionable for detection and response.
Who are the ShinyHunters?
ShinyHunters is an extortion group that emerged in 2020. Unlike traditional ransomware groups that encrypt files, ShinyHunters focuses exclusively on data theft. Their objective is financial where they steal data and sell it on dark web forums. The group is responsible for some of the largest data breaches, often involving hundreds of millions of stolen user records. Their targets include:
- TicketMaster (2024)
- AT&T (2021 & 2024)
- Wattpad(2020)
- Microsoft(2020)
- Tokopedia (2020)
Connection to Scattered Spider/ COM
Since 2020, ShinyHunters has evolved from data theft to sophisticated social engineering and supply chain attacks through their partnership with Scattered Spider—a threat actor group known for advanced social engineering techniques.
Campaigns
In their first two years, the group became known for breaching dozens of high-profile companies simultaneously. They primarily targeted GitHub repositories to find unsecured credentials and API keys. Below are some of the companies they targeted:
- Tokopedia (2020): One of their first major hits, involving the data of 91 million users.
- Microsoft (2020): They claimed to have stolen 500 GB of source code from Microsoft’s private GitHub repositories.
- Wattpad (2020): Stole and leaked a database containing nearly 270 million user records.
SnowFlake Campaign
In mid-2024, ShinyHunters launched a massive campaign targeting Snowflake cloud platform customers. Rather than breaching Snowflake directly, they used stolen credentials to access customer accounts without Multi-Factor Authentication (MFA). Below are some of the companies they attacked during this campaign.
- TicketMaster: They claimed to have stolen data from 560 million customers.
- Santander Bank: Impacted 30 million customers and staff across Spain, Chile, and Uruguay.
- AT&T: Allegedly stolen data on over 110 million customers, leading to a reported $370,000 ransom payment by AT&T to have the data deleted.
The Salesforce “Vishing” Campaign
The group launched a sophisticated campaign targeting Salesforce instances through vishing (voice phishing). ShinyHunters collaborated with Scattered Spider, calling employees while pretending to be IT support. They tricked victims into authorizing a modified version of the Salesforce Data Loader. Companies attacked in this campaign include:
- Goolge & Cisco: Both tech giants were targeted in 2025 and Google confirmed a corporate Salesforce instance was compromised, exposing records for small medium sized businesses.
- Luxury Brands: Brands such as Gucci, Balenciaga, Louis Vuitton, and Dior were targeted as well as ShinyHunters took VIP customer data.
Supply Chain & SaaS integration
In late 2025, ShinyHunters began targeting the software supply chain by compromising developer tools and third-party integrations.
- RedHat /GitLab: They claimed responsibility for breaching a GitLab server used by Red Hat, potentially accessing thousands of code repositories and “Customer Engagement Reports”.
- Salesloft/ Drift: They exploited stolen OAuth tokens from Salesloft’s chatbot integrations to again access to hundreds of corporate Salesforce environments worldwide.
Vishing attacks on Okta, Microsoft Entra, Google
On January 23, 2026, ShinyHunters confirmed to BleepingComputer their involvement in social engineering attacks targeting SSO credentials for Okta, Microsoft Entra, and Google. The campaign's primary objective is to compromise employee SSO accounts and leverage them as entry points into other SaaS platforms to exfiltrate sensitive data.
In this attack, the attacker impersonates IT support over the phone and directs the victim to phishing sites that mimic corporate login portals. Users are tricked into entering their credentials and MFA codes in real time, allowing attackers to hijack the SSO session. Once compromised, attackers can view connected applications and harvest data from platforms such as:
- Microsoft 365
- Google Workspace
- Salesforce
- Slack
- Dropbox
- Zendesk
What is ShinySp1d3r?
ShinySp1d3r is a Ransomware-as-a-Service (RaaS) platform developed by ShinyHunters and Scattered Spider. Before creating their own tool, these groups relied on encryptors from established ransomware operations, including:
- ALPHV/BlackCat
- Qilin
- RansomHub
- Dragonforce
ShinyS1d3r Capabilities
ShinyHunters developed this encryptor from scratch. Key features include:
- Hooking with EtwEventWrite function to prevent data from being logged to the Windows Event Viewer.
- Kills processes that keep a file open and prevent it from being encrypted by iterating over processes with handles to the file, then killing them.
- Uses a “forceKillUsingRestartManager” function that uses the Restart Manager API, but this feature is not implemented yet.
- Fills free space on a drive by writing random data into files called ‘[wipe-random].tmp’. This is done to overwrite any detected files, making them more challenging.
- Kills a hard-coded list of processes and services
- Checks available memory to calculate optimal encryption.
ShinySP1D3R analysis
| File Name | C:\Windows\i3yylg.exe |
|---|---|
| SHA256 | 3bf53cddf7eb98d9cb94f9aa9f36c211a464e2c1b278f091d6026003050281de |
| MD5 | 60f0d614ee1cfcfd237f6705a33765c3 |
| File Size | 4.46 MB |
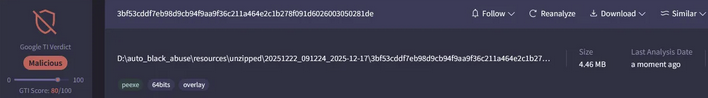
When loaded in Detect It Easy, the file appears as a PE64 executable built for AMD64 architecture. The malware is written in Go and includes a signing tool that uses Windows Authenticode, a Microsoft technology that verifies the origin and integrity of software binaries like .exe, .dll, and .sys files through digital signatures.
Authenticode provides assurance when downloading files. Windows checks the signature to verify two things: the software's identity (confirming it comes from the legitimate publisher) and its integrity (ensuring the code hasn't been tampered with). However, in this case, the file is malicious,attackers applied a valid signature to the malicious file to bypass security tools.
The file uses signing protocol 2.0, which supports robust hashing algorithms like SHA-256. This keeps the signature valid even after the certificate expires. The file also uses a packer.
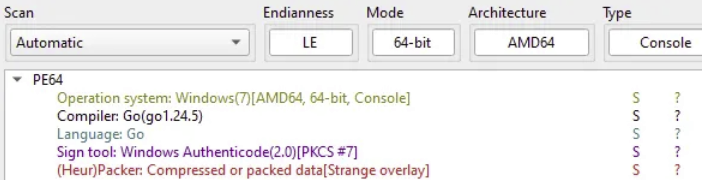
Entropy
Analyzing the file's entropy shows that 76 percent of the file is unpacked. All PE header sections remain unpacked. However, a packed overlay exists with a high entropy of 7.62832.
Looking back at the previous image showing the file details, the packer was detected on the PE file's overlay. The compressed section uses a valid digital signature—specifically signed by a certificate associated with "WinAuth" in PKCS#7 (Public Key Cryptography Standards #7) format. This is how it evades security tools.
Investigation
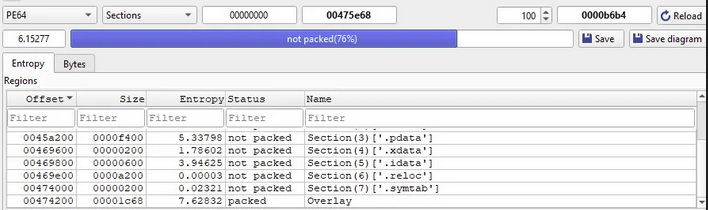
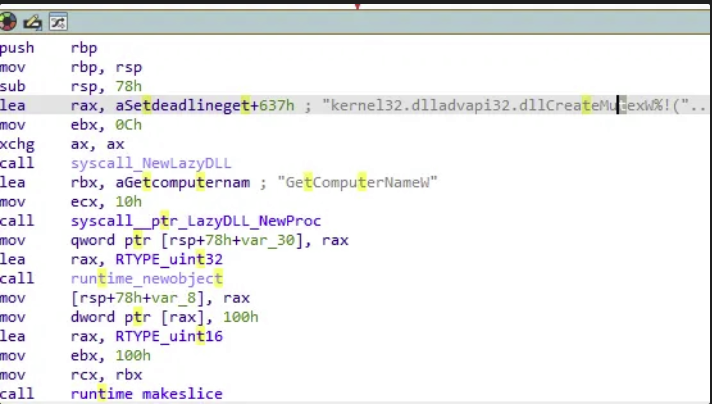
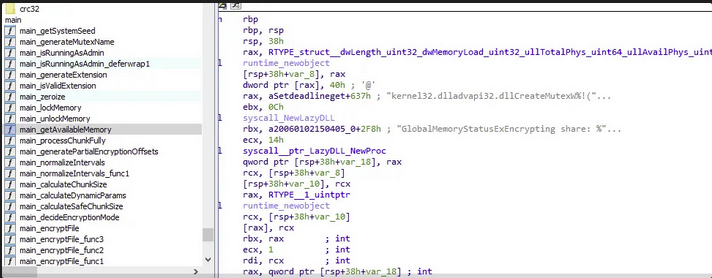
I examined the file's execution flow and found the main function. The first function, main_getSystemSeed, collects machine information and creates a mutex after loading two DLL files onto the target system.
This process loads two DLL files:
- kernel32.dll
- advapi32.dll
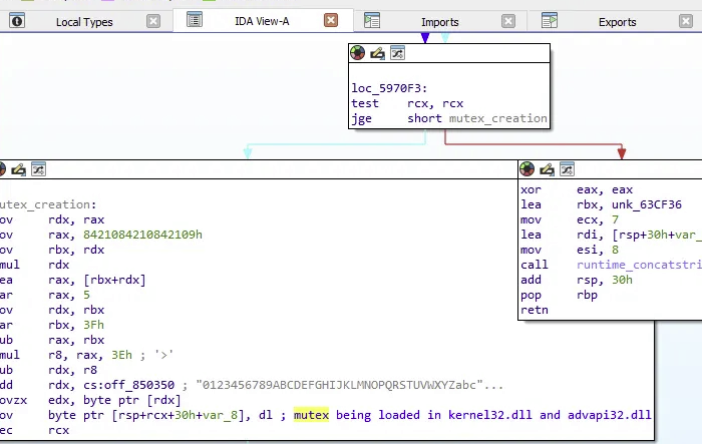
Mutex Creation
In the main_generateMutexName function, the malware calls main_GetSystemSeed to gather specific information about the infected machine before creating the mutex. It then jumps to function loc_5970F3, where it calls runtime_concatstring2 to combine two strings and create the mutex.
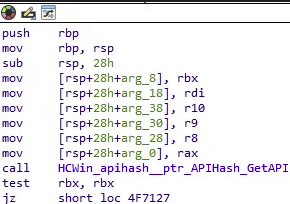
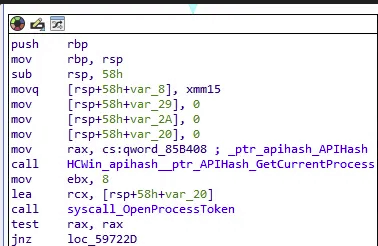
Running as Admin /API hashing
When threat actors elevate their privileges and run as an administrator, a function called main_isRunningAsAdmin executes. The attackers use a technique called API hashing. Normally, when a program needs to perform an action—like "Get the current process", it calls a Windows function by name: GetCurrentProcess. Antivirus and EDR tools flag suspicious files that call GetCurrentProcess followed by ReadProcessMemory.
However, threat actors found a solution—it's called API hashing. This technique works by converting the function name "GetCurrentProcess" into a numerical hash. The malware then searches through the computer's memory for a function that matches that number.
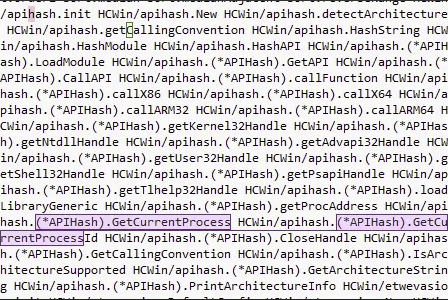
In this case, the malware has a function called HCWin_apihash_ptr_APIHash_GetCurrentProcess that loads kernel32.dll and advapi32.dll, then fetches a process where it calls GetCurrentProcess. The malware uses API hashing to invoke this function with a unique hash, bypassing security defenses from EDR, SIEM, and antivirus tools.
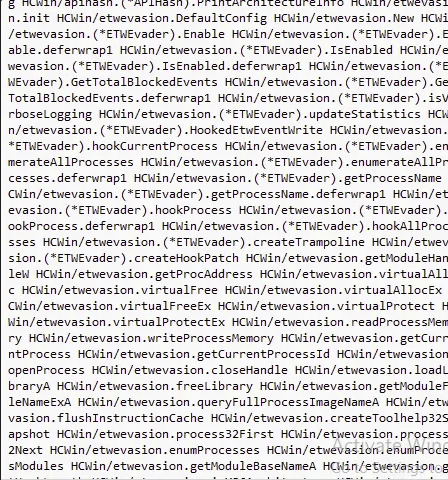
I couldn't find the functions the malware was calling in IDA Pro, so I used Malcat to identify the API functions:
- callx86
- callx64
- callARM32
- callARM64
- getKernel32Handle
- getShell32Handle
- getNtdllHandle
- getAdvapi32Handle
- GetCurrentProcessId
- CloseHandle
- GetCallignConvention
- IsArchitectureSupported
- GetArchitectureString
- PrintArchitectureInfo
Instead of calling ReadProcessMemory, the malware uses the hash for the following Windows API functions to gather additional information about the infected system's architecture.
Elevating Privileges/ syscall_OpenProcessToken
The malware makes a syscall to the Windows API function OpenProcessToken, which opens the access token associated with a process. The threat actors use this to query token privileges and elevate to Admin.
Preventing logs from being logged in Event Viewer
One of the malware's unique capabilities is preventing logs from being recorded in Windows Event Viewer. Further into the execution flow, I found another function called main_isRunningAsAdmin_deferwrap1.
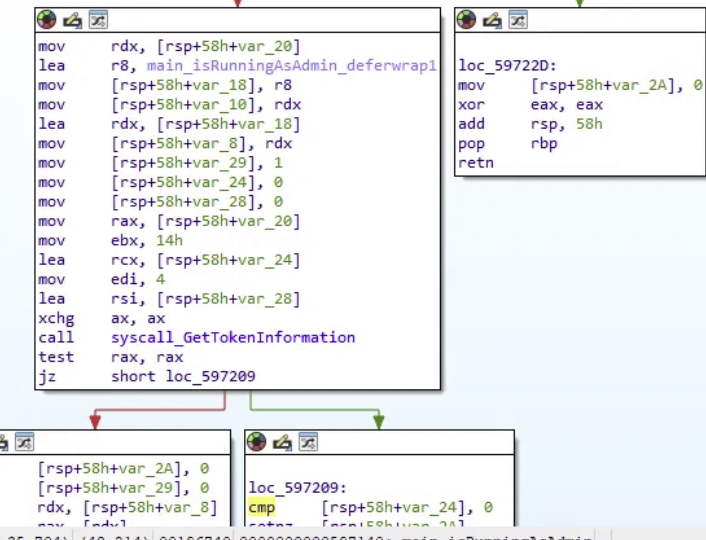
This wrapper function is designed to evade security tools. Analysis in Malcat reveals that ShinyHunters uses ETWEvader to hook the EtwEventWrite function, which neutralizes system logging. This allows them to execute data-stealing tools in a "wrapped" state and exfiltrate gigabytes of data without triggering alerts.
The attacker calls the following functions:
- GetTotalBlockedEvents
- isVerbsoeLogging
- updateStatistics
- hookCurrentProcess
- enumerateAllProcesses.deferwrap1
- HookProcess.deferwrap1
- getModuleHandleW
- virtualAllocEx
- getCurrentProcessID
- flushInstructionCache
Additionally, while the malware encrypts files, the main_lockMemory function executes and clears Windows events. This function locks specific API functions in memory to either redirect them or prevent the system from logging the ransomware activities, such as shadow copy deletion or file encryption.
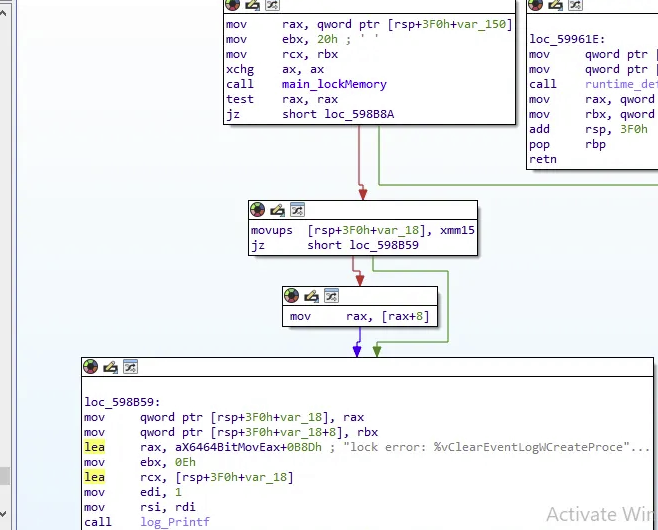
Gathering Available Memory
Looking at the execution flow, the malware calls NewLazyDLL. Within this function is another function named GlobalMemoryStatusExEncrpyting. This is not a standard Windows command. GlobalMemoryStatusEx is a function that software uses to query the operating system for current memory usage information. ShinyHunters performs a memory check on the system before encrypting data to ensure there is enough space to process it.
Data Obfuscation
In the main_porcessChunkFully function, ShinyHunters uses the ChaCha20 XOR stream cipher to obfuscate data and hinder analysis. The malware encrypts the data in chunks of 8 bytes, then moves to the next 8-byte block.
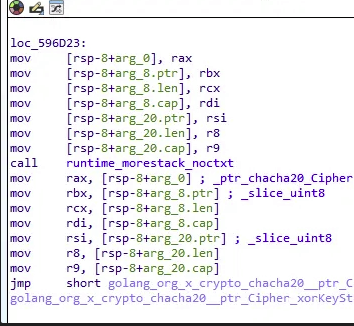
Partial Encryption
During encryption, ShinySp1d3r uses partial encryption to improve speed. Instead of encrypting entire files, it encrypts files based on different chunk sizes. The malware uses a ChaCha20 XOR stream cipher to encrypt files in chunks of 8 bytes of data.
Looking at the execution flow for main_generatedPartialEncryptionOffsets, the malware uses the functions cvtsi2sd (convert integer to double) and mulsd (multiply scalar double) to calculate what percentage or ratio of the file to encrypt. The malware then calls the math_min function to ensure that the calculated encryption chunk does not exceed the actual file size or a hard-coded safety limit.
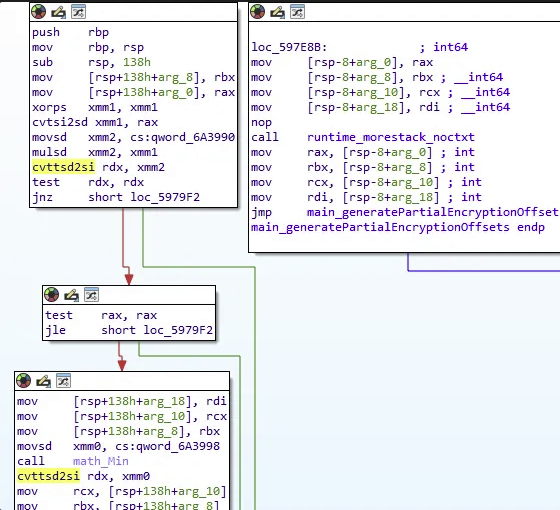
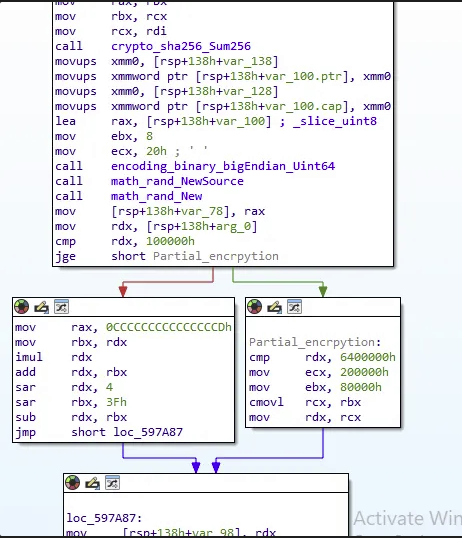
The malware calls crypto_sha256_Sum256 to generate a 32-byte hash, then uses encoding_binary_bigEndian_Uint64 to convert it into a numeric format that Go can process. To initialize partial encryption, it calls math_rand_NewSource followed by math_rand_New, randomizing which files will be analyzed and partially encrypted.
The malware has a threshold set at 100000h (1MB) to compare files. If a file is less than 1MB, it is encrypted entirely. If the file is greater than 1MB, the malware jumps to the Partial Encryption function, where it encrypts specific "chunks" of large files to increase attack speed.
Encryption
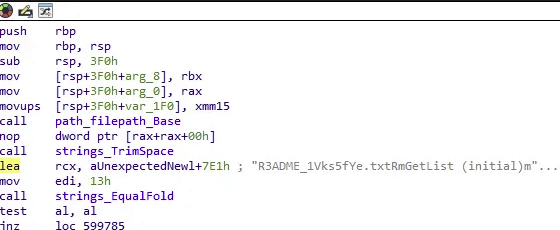
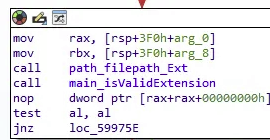
The encryptFile function identifies target files and prepares the ransom note. It calls path_filepath_Ext and main.isValidExtension to determine whether a file should be encrypted or skipped based on its type. The strings_EqualFold function performs case-insensitive filename checks, ensuring the malware doesn't encrypt its own ransom note or critical system files.
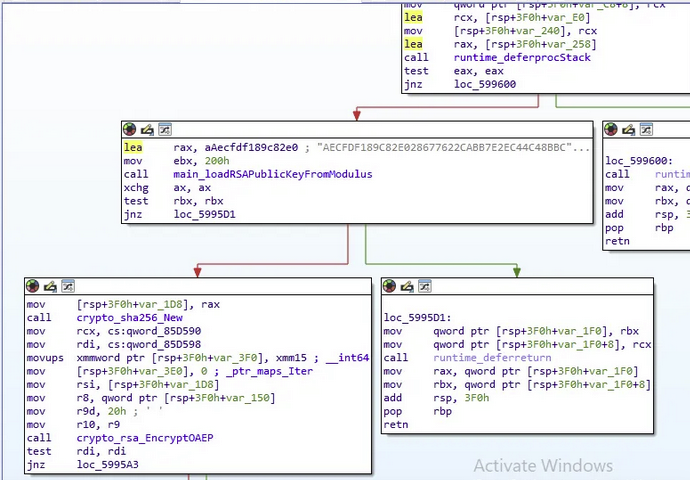
In addition to encryption, the malware loads a hard coded RSA public key modulus and passes it to the main_loadRSAPublicKeyFromModulus function. The malware uses RSA-OAEP to re-encrypt the files, ensuring only the attacker (who holds the private key) can decrypt them.
Conclusion
ShinySp1d3r represents a significant evolution in ShinyHunters' operational capabilities, demonstrating the group's transition from pure data theft to sophisticated ransomware operations. This ransomware variant showcases advanced evasion techniques and technical sophistication that make it a critical threat to monitor.
Key Threat Characteristics:
Multi-Stage Attack Chain: ShinyHunters leverages social engineering through vishing and phishing campaigns to gain initial access, often exploiting exposed credentials in GitHub repositories and compromised API keys from platforms like Salesforce and Snowflake.
Advanced Defense Evasion: The malware employs API hashing to bypass EDR and antivirus detection, uses ETW evasion to prevent Windows event logging, and implements memory locking techniques to hide malicious activities.
Efficient Encryption Strategy: ShinySp1d3r uses ChaCha20 XOR stream cipher for data obfuscationcombined with RSA-OAEP encryption, and employs partial encryption techniques that target specific chunks of large files to maximize speed while maintaining impact.
High-Profile Targeting: The group has demonstrated capability to compromise major organizations including TicketMaster, AT&T, Microsoft, and Tokopedia, with breaches involving hundreds of millions of user records.
Continuous Monitoring Rationale:
ShinyHunters warrants continuous monitoring due to their evolving tactics and proven track record of high-impact breaches. The group's connection to Scattered Spider/COMindicates sophisticated organizational capabilities and access to advanced technical resources. Their shift from data-only theft to ransomware operations represents an escalation in threat level that requires proactive defense measures and ongoing intelligence gathering.
The detailed technical analysis of ShinySp1d3r's API hashing, privilege escalation, ETW tampering, and encryption mechanismsprovides critical indicators for detection and response. Organizations should implement the comprehensive mitigations outlinedand maintain vigilance for the specific TTPs documented, as ShinyHunters continues to refine their techniques and expand their target portfolio.
Mitigations
Prevent Initial Access & Social Engineering
Combat Vishing/Phishing Attacks:
- Implement strict verification procedures for IT support calls - never authorize software installations based on phone requests alone.
- Establish out-of-band verification protocols (callback to known internal numbers).
- Conduct regular security awareness training focused on social engineering tactics used by ShinyHunters/Scattered Spider.
- Deploy phishing-resistant MFA (FIDO2/WebAuthn) rather than SMS or app-based MFA.
Secure Credentials & API Access:
- Enforce MFA on all accounts, especially cloud platforms like Salesforce and Snowflake.
- Implement credential scanning tools to detect exposed API keys and tokens in GitHub repositories.
- Rotate credentials regularly and immediately upon suspected compromise.
- Use OAuth token monitoring and anomaly detection for SaaS integrations.
Network & Endpoint Defenses
Block Execution & Lateral Movement:
- Implement application whitelisting to prevent unauthorized executables.
- Deploy Endpoint Detection and Response (EDR) solutions with behavioral analysis.
- Enable Windows Defender Application Control or AppLocker.
- Restrict execution from common ransomware staging directories (temp folders, user profiles).
Detect API Hashing & Process Manipulation:
- Monitor for suspicious API resolution patterns and dynamic function loading.
- Alert on processes calling GetCurrentProcess followed by OpenProcessToken.
- Detect ETW (Event Tracing for Windows) tampering attempts.
- Monitor for EtwEventWrite function hooking.
Memory & System Integrity Protection
Prevent ETW Evasion:
- Implement kernel-level ETW protection.
- Use Sysmon with ETW tampering detection rules.
- Deploy memory integrity features like Hypervisor-Protected Code Integrity (HVCI).
- Monitor for VirtualAllocEx and WriteProcessMemory calls targeting ntdll.dll.
Block Privilege Escalation:
- Implement least privilege access controls.
- Monitor for suspicious OpenProcessToken and AdjustTokenPrivileges calls.
- Enable Windows Defender Credential Guard.
- Restrict admin rights and use privileged access management (PAM) solutions.
File System & Data Protection
Mitigate Encryption Impact:
- Deploy Controlled Folder Access in Windows Defender.
- Implement file integrity monitoring (FIM) solutions.
- Enable Volume Shadow Copy Service (VSS) protection and monitor for deletion attempts.
- Maintain offline, immutable backups following the 3-2-1 rule.
Detect Encryption Behavior:
- Monitor for high volumes of file modifications in short time-frames.
- Alert on creation of (.tmp) files with random names (wipe-random patterns).
- Detect processes accessing large numbers of files sequentially.
- Monitor for ChaCha20 or RSA-OAEP encryption library loading.
Process & Service Hardening
Prevent Process/Service Termination:
- Use protected process light (PPL) for critical security services.
- Monitor for Restart Manager API abuse.
- Alert on mass process termination events.
- Implement tamper protection for security software.
Block Common Ransomware Behaviors:
- Monitor and restrict access to kernel32.dll and advapi32.dll from suspicious. processes
- Detect and block shadow copy deletion commands (vssadmin, wmic).
- Monitor for bcdedit modifications to boot configuration.
- Alert on attempts to disable Windows Defender or other security tools.
Supply Chain & Third-Party Risk
Secure Development Pipeline:
- Implement code signing verification and certificate pinning
- Monitor for Authenticode signature anomalies (valid signatures on unexpected files)
- Scan for packed executables with high entropy overlays
- Secure GitLab/GitHub servers and implement branch protection rules
Vendor & Integration Security:
- Audit third-party SaaS integrations and OAuth permissions.
- Monitor Salesforce Data Loader modifications.
- Implement zero-trust architecture for cloud services.
- Review and restrict API access tokens regularly.
Detection & Response
SIEM/Log Analysis Rules:
- Alert on multiple failed authentication attempts followed by success.
- Monitor for unusual data exfiltration volumes to external destinations.
- Detect after-hours access to sensitive data repositories.
- Track suspicious PowerShell, cmd, or Go binary executions.
Incident Response Preparation:
- Develop and test ransomware-specific incident response playbooks.
- Establish communication protocols for ransom scenarios..
- Maintain offline forensic images of critical systems.
- Create network segmentation plans to contain outbreaks.
Specific IOCs to Block
Hash-Based Blocking:
- SHA256:
3bf53cddf7eb98d9cb94f9aa9f36c211a464e2c1b278f091d6026003050281de - MD5:
60f0d614ee1cfcfd237f6705a33765c3 - Monitor for PE64 executables with WinAuth signatures and high overlay entropy (>7.6)
Behavioral Indicators:
- Executables named with random lowercase letters (pattern:
i3yylg.exe) - Go-compiled binaries with Authenticode signatures.
- Mutex creation following kernel32.dll and advapi32.dll loading.
These layered defenses should significantly reduce your attack surface against ShinySp1d3r and similar ransomware operations.
Tactics Techniques and Procedures
| Tactic | Technique ID | Description |
|---|---|---|
| Initial Access | T1566 - Phishing | Uses vishing/phishing attacks and social engineering to gain initial access |
| Initial Access | T1078 - Valid Accounts | Exploits exposed credentials and API keys found in GitHub repositories |
| Defense Evasion | T1027 - Obfuscated Files or Information | Uses API hashing to obfuscate malicious API calls |
| Defense Evasion | T1562.001 - Impair Defenses: Disable or Modify Tools | Tampers with ETW (Event Tracing for Windows) to evade detection |
| Defense Evasion | T1055 - Process Injection | Uses VirtualAllocEx and WriteProcessMemory to inject code into processes |
| Privilege Escalation | T1134 - Access Token Manipulation | Uses OpenProcessToken and AdjustTokenPrivileges to escalate privileges |
| Impact | T1486 - Data Encrypted for Impact | Encrypts files using ChaCha20 and RSA-OAEP encryption |
| Impact | T1489 - Service Stop | Terminates processes and services using Restart Manager API |
| Impact | T1490 - Inhibit System Recovery | Deletes shadow copies using vssadmin and wmic commands |




